APPLICATIONS
HOT NEWS
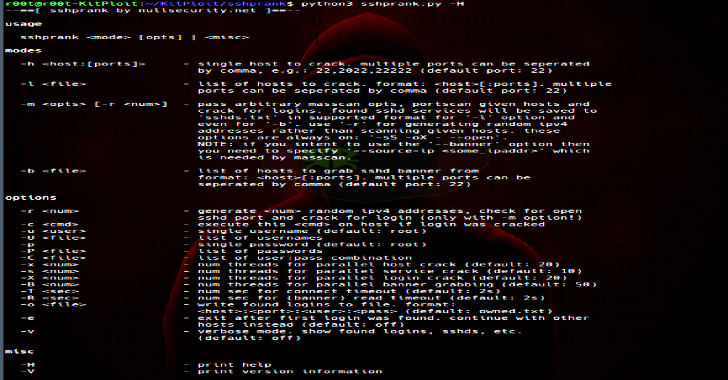
SSHPrank : A Fast SSH Mass-Scanner, Login Cracker & Banner Grabber
SSHPrank is a fast SSH mass-scanner, login cracker and banner grabber tool using the python-masscan and shodan module.
Usage
Notes
quick'n'dirty codesshprank is already packaged and available...
© kalilinuxtutorials.com 2025