- Android
- Apple
- Applications
- Blog
- Cyber security
- Database Assessment
- Exploitation Tools
- Forensics
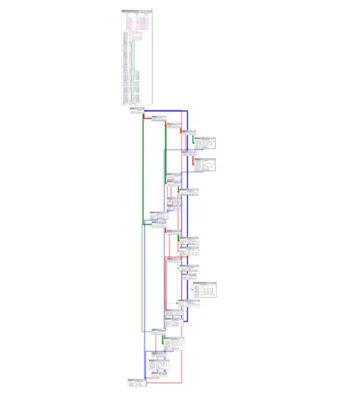
- Hacking Tools
- Information Gathering
- Kali Linux
- Linux
- Malware
- OSINT
- Password Attacks
- Pentesting Tools
- Phishing
- Post Exploitation
- Security Hacker
- Sniffing/Spoofing
- software
- Stress Testing
- TECH
- Tech today
- Tutorials
- VPN
- Vulnerability Analysis
- Web Application Analysis
- Windows
- Wireless Attacks
APPLICATIONS
HOT NEWS
Rspack : Revolutionizing Web Development With Rust-Powered Bundling
Rspack is a cutting-edge JavaScript bundler written in Rust, designed to deliver high performance and compatibility with the Webpack ecosystem.
Developed by ByteDance, Rspack...
We provide you with the latest Kali Linux & Penetration testing tools.
Contact us: admin@kalilinuxtutorials.com
© @Kali Linux Tutorials - 2025