By readapting the safetydump rust library (many thanks to the author!!!), I have been able to EASILY bypass all the countermeasures put in place by most EDRs, except Kaspersky EDR, and TrendMicro (new detection, from a couple hours ago)
dbghelp!MiniDumpWriteDump with a custom callback could be used, until a year ago, to bypass most antivirus and EDR solutions.
Now, most of them EASILY recognize statically or behaviorally the system API usage pattern for programs written in languages such as C++, Delphi, and C#. (it could be possible anyway thanks to undocumented NtOpenProcessEx but that’s another story.)
If you have a Go implementation, please give me feedback. I’m on it but still have some bugs related to memory size
I suspect that there is still no way to monitor the MiniDumpWriteDump callback, and all the protection against a possible credential dump via this technique is then entrusted to machine learning detections.
Usage
GUI

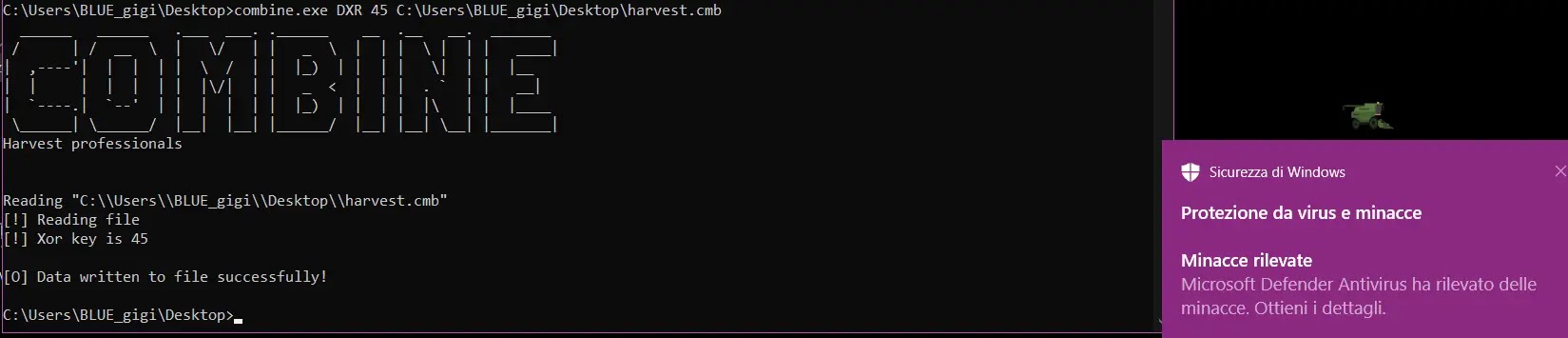
CMD

DECRYPT
Disclaimer
I am not responsible for any improper use of this tool. This is meant for research and security testing purposes.






.webp)





.webp)