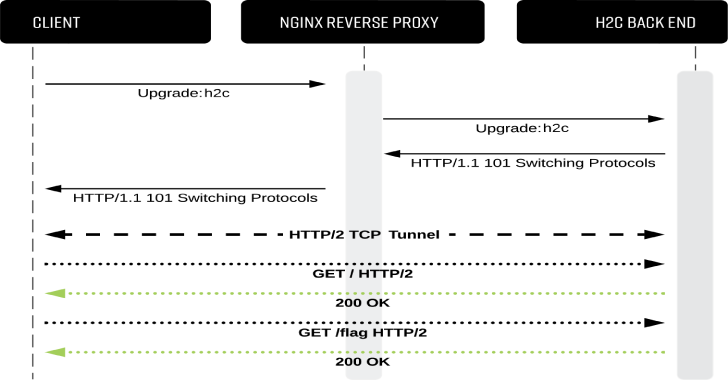
h2cSmuggler smuggles HTTP traffic past insecure edge-server proxy_pass configurations by establishing HTTP/2 cleartext (h2c) communications with h2c-compatible back-end servers, allowing a bypass of proxy rules and access controls.
See my detailed write-up below for:
- Technical breakdown of the vulnerability
- Insecure-by-default services
- Remediation guidance
Here: https://labs.bishopfox.com/tech-blog/h2c-smuggling-request-smuggling-via-http/2-cleartext-h2c
How to test?
Any proxy endpoint that forwards h2c upgrade headers can be affected. Because h2c is intended to be performed only on cleartext channels, detection on HTTPS services often yields true positives.
By contrast, HTTP services may result in false positives. For example, h2c-enabled proxies may respond to the upgrade instead of forwarding it to an h2c back end.
Use the --scan-list option to test one or more web servers to look for affected proxy_pass endpoints. Consider using a list of directories discovered from directory enumeration, such as:
urls.txt
https://www.example.com/
https://www.example.com/api/
https://www.example.com/auth/
https://www.example.com/admin/
https://www.example.com/payments/
…omitted for brevity…
Run h2cSmuggler with the list of endpoints and a total number of threads:
./h2csmuggler.py --scan-list urls.txt --threads 5
Or, an individual test can be performed with:
./h2csmuggler.py -x https://www.example.com/api/ --test
- Detecting with other popular tools:
- Burp Extension (Active Scan check)
- Nuclei-Template (Coming soon! Requires this issue to be fixed)
Exploitation
Once you have identified an affected endpoint that can be used for tunneling, you can now access or brute-force internal endpoints on the back-end server and provide custom verbs or headers. In the demo below, we demonstrate accessing an internal /flag endpoint by using h2c smuggling to bypass proxy deny rules.
To remediate, do not forward user-supplied values for Upgrade or Connection headers. See the technical post for additional guidance.
Install Instructions
The only dependency is the Python hyper-h2 library:
pip3 install h2
Test Environment & Demo
The test environment will allow you to experiment with h2cSmuggler in a controlled environment. docker-compose will simulate three chains of proxies that lead to an h2c-enabled Golang back end:
TCP port: Description
======== ===========
8000: HTTP h2c backend
8001: HAProxy -> h2c backend (Insecure default configuration)
8002: nginx -> h2c backend (Insecure custom configuration)
8003: Nuster -> HAProxy -> h2c backend (Insecure configuration with multiple layers of proxies)
[1] Generate Certificates and spin up the environment with docker-compose:
# Generate certs
./configs/generate-certificates.sh
# Activate services
docker-compose up
All of the proxies deny access to the /flag endpoint accessible on the h2c back end. Let’s attempt to access the forbidden endpoint via the HAProxy server running on port 8001:

We can use h2cSmuggler to confirm the proxy’s insecure configuration using --test (or -t):
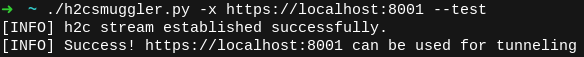
Now, let’s use h2cSmuggler to perform an h2c upgrade, tunnel our HTTP/2 traffic through the proxy, and request the /flag endpoint from the back end, bypassing the proxy’s access control:

For a deeper explanation of what is happening, check out the technical writeup.
Usage
h2cSmuggler uses a familiar curl-like syntax for describing the smuggled request:









.png)
.webp)

.png)