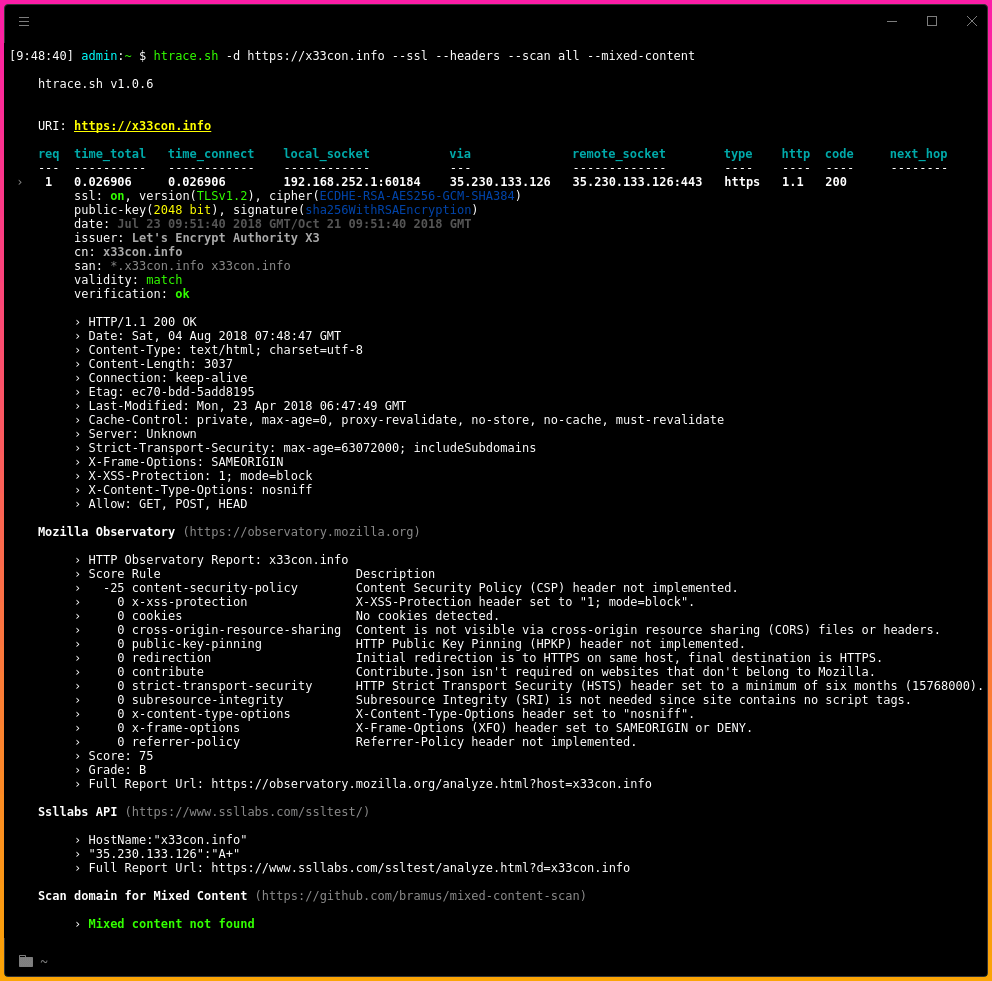
htrace.sh simple shell script to debugging http/https traffic tracing, response headers and mixed-content. Scanning domain using Nmap NSE Library. Support external security tools: Mozilla Observatory and SSL Labs API.
htrace.sh is a shell script that allows you to validate your domain configuration and catch any errors (e.g. redirect loops). It also displays basic information about the ssl configuration (if available), response headers, checks for mixed content and performs security scans using Nmap scripts and great external tools such as Ssllabs or Mozilla Observatory.
Also Read WinPwnage – Elevate, UAC Bypass, Privilege Escalation, dll Hijack Techniques
Functions
It is useful for:
- Checking properly domain configuration (web servers/reverse proxies)
- redirects analysis, e.g. to eliminate redirect loops
- checking response headers for each request
- checking basic ssl configuration
- validation of the certificates (date, cn, san) and verification ssl connection
- scanning domain for Mixed Content
- scanning domain using Nmap NSE Library
- scanning domain with external security tools: Mozilla Observatory and SSL Labs API
Note: Before use htrace.sh please see Requirements.
How To Use htrace.sh
It’s simple:
# Clone this repository
git clone https://github.com/trimstray/htrace.sh
# Go into the repository
cd htrace.sh
# Install
./setup.sh install
# Run the app
htrace.sh --domain https://google.com
- symlink to
bin/htrace.shis placed in/usr/local/bin- man page is placed in
/usr/local/man/man8
External Tools
htrace.sh support external tools for security scans:
- Mozilla Observatory – cli version of observatory.mozilla.org
with params:--format=report --rescan --zero --quiet - Ssllabs – command-line reference-implementation client for SSL Labs API
with params:-quiet -grade - mixed-content-scan – cli tool for check HTTPS-enabled website for Mixed Content
with params:-user-agent \"$_user_agent\" --no-check-certificate - Nmap NSE Library – provide automated security scans with Nmap
with scripts:- http-auth-finder
- http-chrono
- http-cookie-flags
- http-cors
- http-cross-domain-policy
- http-csrf
- http-dombased-xss
- http-git
- http-grep
- http-internal-ip-disclosure
- http-jsonp-detection
- http-malware-host
- http-methods
- http-passwd
- http-phpself-xss
- http-php-version
- http-robots.txt
- http-sitemap-generator
- http-shellshock
- http-stored-xss
- http-unsafe-output-escaping
- http-useragent-tester
- http-vhosts
- http-xssed
- ssl-enum-ciphers
- whois-ip
If you don’t know how to install these tools and where they should be placed, please see in Dockerfile where exactly every step is described.
Note: When scanning for mixed content and nmap scripting engine, remember that it may take a long time before the entire site is checked.
Reports
If you want to generate a report in html format, use the ansi2html.sh tool. A detailed description of use:
htrace.sh -d https://nmap.org -s -h | ansi2html --bg=dark > report.html
Build image
cd htrace.sh/build
docker build --rm -t htrace.sh -f Dockerfile .
Run container
docker run --rm -it --name htrace.sh htrace.sh -d http://nmap.org -h
Parameters
Provides the following options:
htrace.sh v1.0.6
Usage:
htrace.sh <option|long-option>
Examples:
htrace.sh --domain https://example.com
htrace.sh --domain https://example.com -s -h --scan ssllabs
Options:
--help show this message
-d|--domain <domain_name> set domain name
-s|--ssl show ssl server/connection params
-h|--headers show response headers
--scan <all|observatory|ssllabs> scan domain with external security tools
--mixed-content scan website for mixed content
--nse scan website with nmap nse library
--user-agent <val> set 'User-Agent' header
--max-redirects <num> set max redirects (default: 10)
--timeout <num> set max timeout (default: 15)
![]() Credit: GPLv3
Credit: GPLv3