How EDR Killers Bypass Security Tools
Endpoint Detection and Response (EDR) solutions have become a cornerstone of modern cybersecurity, designed to detect and stop advanced threats in real time. However, attackers are increasingly deploying EDR killers, specialized techniques and tools designed to disable, evade, or...
How Does a Firewall Work Step by Step
How Does a Firewall Work Step by Step? What Is a Firewall and How Does It Function?
Introduction
Every second, millions of data packets travel across the internet. These packets carry everything from emails and website data to confidential business transactions....
Top OSINT Tools to Find Emails, Usernames and Passwords
Introduction
In the world of cybersecurity, knowledge is power. One of the most powerful skillsets every ethical hacker, penetration tester, and OSINT researcher must master is the ability to discover digital footprints left behind by individuals and organizations. These footprints...
Admin Panel Dorks : A Complete List of Google Dorks
Introduction
Google Dorking is a technique where advanced search operators are used to uncover information not normally visible in standard search results. One common target is admin panels, login pages for websites, apps, and network devices.
What Are Admin Panel Dorks?
Admin...
WormGPT – A Comprehensive Guide To Setting Up On Various Platforms
WormGPT is a versatile tool designed for creating and managing various types of software across multiple operating systems.
This guide provides detailed instructions on how to install and configure WormGPT on platforms such as Kali Linux, BlackArch Linux, Kali...
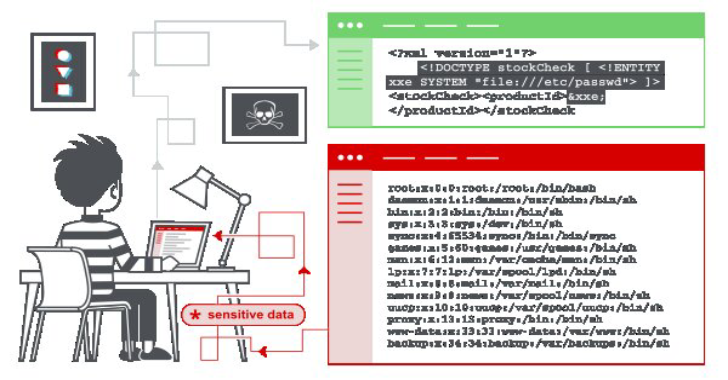
XML External Entity – XXE Injection Payload List
In this section, we'll explain what XML external entity injection is, describe some common examples, explain how to find and exploit various kinds of XXE injection, and summarize how to prevent XXE injection attacks.
What is XML...
WhatsApp OSINT Tool : Advanced Digital Investigation Capabilities
The WhatsApp OSINT Tool is a specialized open-source intelligence (OSINT) tool designed for gathering information from WhatsApp.
Initially developed in 2019, it has since been refined to enhance its functionality and usability.
This tool is particularly useful for digital...
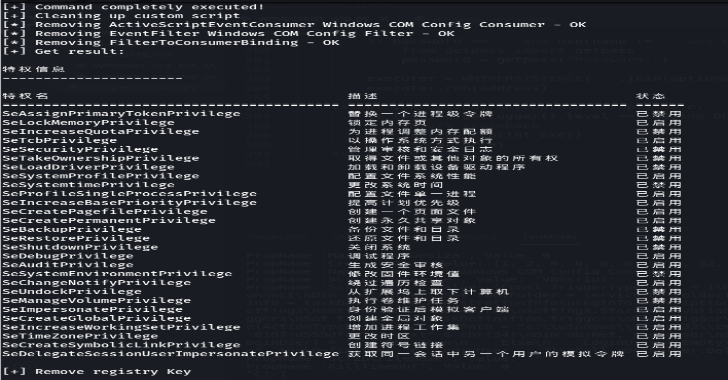
How EDR Killers Bypass Security Tools
Endpoint Detection and Response (EDR) solutions have become a cornerstone of modern cybersecurity, designed to detect and stop advanced threats in real time. However,...
AI-Generated Malware Campaign Scales Threats Through Vibe Coding Techniques
A large-scale malware campaign leveraging AI-assisted development techniques has been uncovered, revealing how attackers are increasingly using “vibe coding” to automate and scale malicious...
How Does a Firewall Work Step by Step
How Does a Firewall Work Step by Step? What Is a Firewall and How Does It Function?
Introduction
Every second, millions of data packets travel across...
Fake VPN Download Trap Can Steal Your Work Login in Minutes
People trying to securely connect to work are being tricked into doing the exact opposite. A new malware campaign shows how a simple search...
This Android Bug Can Crack Your Lock Screen in 60 Seconds
A newly disclosed Android vulnerability is making noise for a good reason. Researchers showed that some phones powered by certain MediaTek chipsets can be...








.webp)