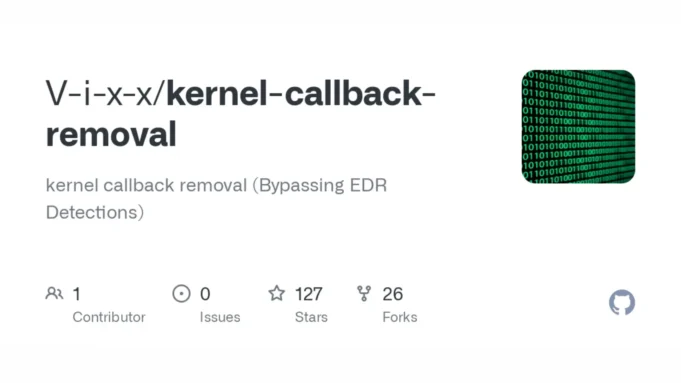
Kernel callbacks are essential components used by Endpoint Detection and Response (EDR) systems to monitor system events, such as process creation, image loading, and registry modifications.
However, attackers have developed techniques to remove these callbacks, effectively blinding EDRs and allowing malicious activities to go undetected.
Tools And Techniques
- Custom Callbacks and Signed Drivers: Tools like CheekyBlinder utilize signed, vulnerable drivers to enumerate and modify kernel callbacks. This allows attackers to remove the sources of telemetry used by EDRs, rendering them ineffective.
- Kernel Notify Routines Callback Bypass: This involves overwriting callback functions with KCFG-compliant functions that simply return, evading detections that monitor changes at the callback array level.
- MiniFilter File Callback Bypass: MiniFilters are used by EDRs to intercept file system I/O operations. Bypassing these can prevent EDRs from detecting file-related malicious activities.
- Windows Kernel Debugger: While not ideal for stealth, the Windows Kernel Debugger can be used to remove kernel callbacks, though its presence may trigger alerts.
Prerequisites And Tools Used
- Assembly Understanding: Essential for manipulating low-level code.
- C Programming Familiarity: Required for developing custom tools.
- WinDbg and IDA: Used for debugging and reverse engineering kernel components4.
- Windows Kernel Exploitation Knowledge: Necessary for understanding how to bypass kernel-level protections.
This topic is aimed at both pentesters and defenders, providing insights into how attackers bypass EDR kernel implementations.
It allows researchers to create custom tools for bypassing signature-based detections and understand the technical aspects of EDR bypassing.
These techniques are for educational purposes only. Unauthorized use against systems without explicit permission is strictly prohibited.
Kernel callbacks removal is a sophisticated technique used to evade EDR detections, highlighting the need for robust kernel-level protections to maintain security infrastructure integrity.
As attackers continue to innovate, defenders must stay vigilant and adapt their strategies to counter these evolving threats.






.jpg)