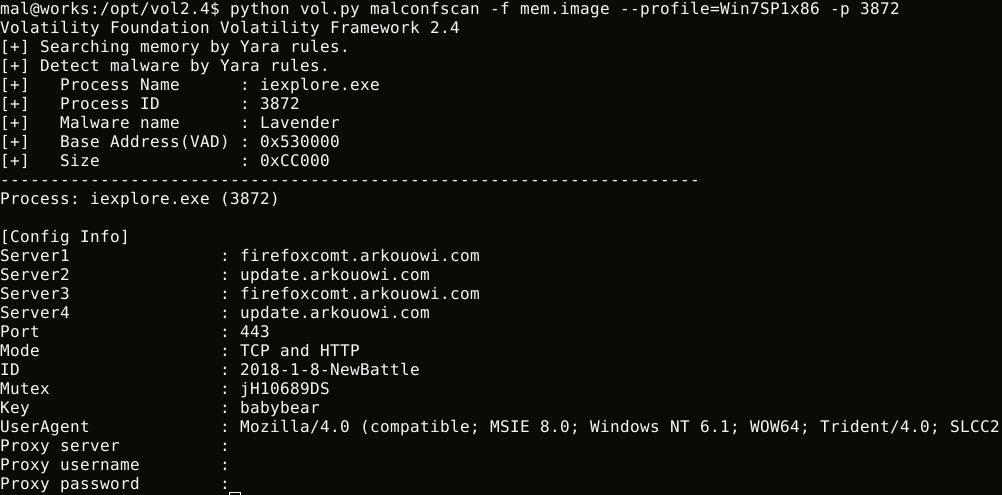
MalConfScan is a Volatility plugin extracts configuration data of known malware. Volatility is an open-source memory forensics framework for incident response and malware analysis. This tool searches for malware in memory images and dumps configuration data. In addition, this tool has a function to list strings to which malicious code refers.
Supported Malware Families
It can dump the following malware configuration data, decoded strings or DGA domains:
- Ursnif
- Emotet
- Smoke Loader
- PoisonIvy
- CobaltStrike
- NetWire
- PlugX
- RedLeaves / Himawari / Lavender / Armadill / zark20rk
- TSCookie
- TSC_Loader
- xxmm
- Datper
- Ramnit
- HawkEye
- Lokibot
- Bebloh (Shiotob/URLZone)
- AZORult
- NanoCore RAT
- AgentTesla
- FormBook
- NodeRAT (https://blogs.jpcert.or.jp/ja/2019/02/tick-activity.html)
- njRAT
- TrickBot
- Remcos
- QuasarRAT
- Pony
Also Read – Penta : Open Source All-In-One CLI Tool To Automate Pentesting
It has a function to list strings to which malicious code refers. Configuration data is usually encoded by malware. Malware writes decoded configuration data to memory, it may be in memory. This feature may list decoded configuration data.
Install packages
If you do not have Yara, please check this page and install it.
Volatility only supports Python2. If you do not have Python2, please install it.
- Download the Volatility source code.
- Extract the Volatility source code from the zip or tar.gz file.
$ wget http://downloads.volatilityfoundation.org/releases/2.6/volatility-2.6.zip
$ unzip volatility-2.6.zip
or cloning from Github.
$ git clone https://github.com/volatilityfoundation/volatility.git
- Clone MalConfScan Github repository
$ git clone https://github.com/JPCERTCC/MalConfScan.git
- Install Python requirements
$ pip install -r MalConfScan/requirements.txt
- Copy it to Volatility Plug-in folder
$ cd MalConfScan
$ cp -R malconfscan.py utils yara [Extract Volatility Folder]/volatility/plugin/malware
For Volatility on Linux, please refer to the Volatility wiki.
It has two functions malconfscan and malstrscan.
Export known malware configuration
$ python vol.py malconfscan -f images.mem –profile=Win7SP1x64
$ python vol.py malstrscan -f images.mem –profile=Win7SP1x64
Malware configuration data can be dumped automatically by adding it to Cuckoo Sandbox. If you need more details on Cuckoo and the tool integration, please check MalConfScan with Cuckoo.