APPLICATIONS
HOT NEWS
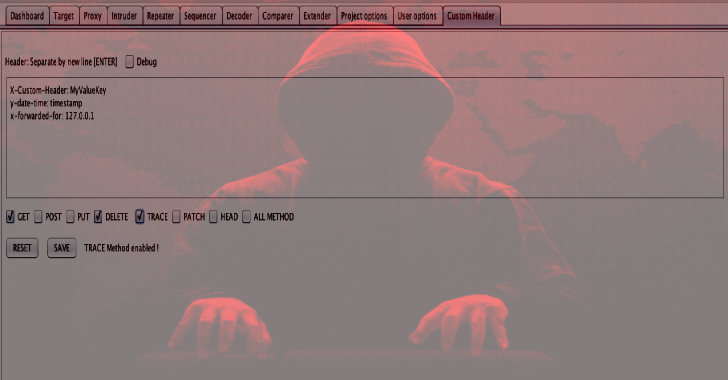
Custom Header : Automatic Add New Header To Entire BurpSuite HTTP...
Custom Header is a Burp Suite extension allows you to customize header with put a new header into HTTP REQUEST BurpSuite (Scanner, Intruder, Repeater,...
© kalilinuxtutorials.com 2025





.png)