APPLICATIONS
HOT NEWS
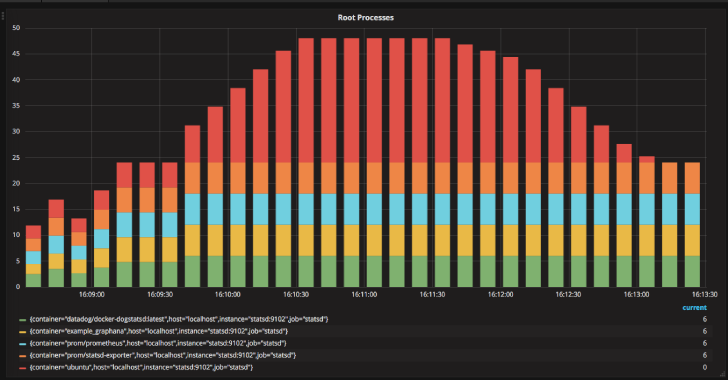
Cnitch : Container Snitch Checks Running Processes Under The Docker Engine
Cnitch (snitch or container snitch) is a simple framework and command line tool for monitoring Docker containers to identify any processes which are running...
© kalilinuxtutorials.com 2025