APPLICATIONS
HOT NEWS
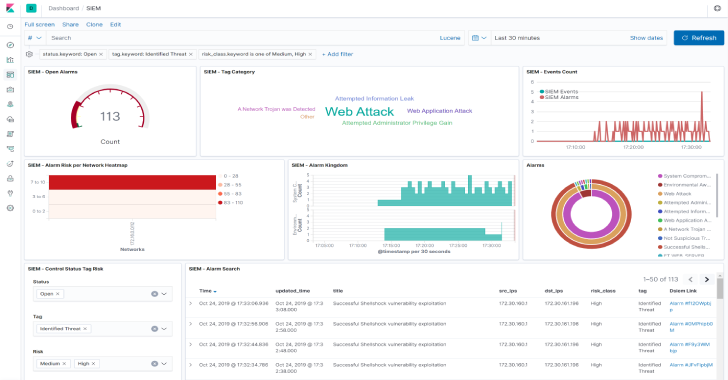
Dsiem : Security Event Correlation Engine For ELK Stack
Dsiem is a security event correlation engine for ELK stack, allowing the platform to be used as a dedicated and full-featured SIEM system.
It provides...
© kalilinuxtutorials.com 2025