APPLICATIONS
HOT NEWS
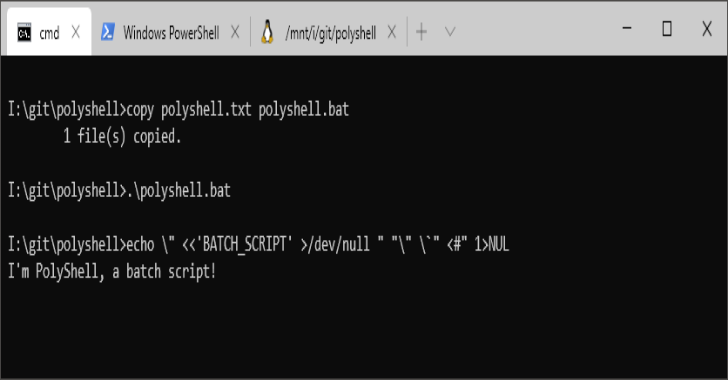
Polyshell : A Bash/Batch/PowerShell Polyglot
PolyShell is a script that's simultaneously valid in Bash, Windows Batch, and PowerShell. This makes PolyShell a useful template for penetration testing as it...
© kalilinuxtutorials.com 2025