APPLICATIONS
HOT NEWS
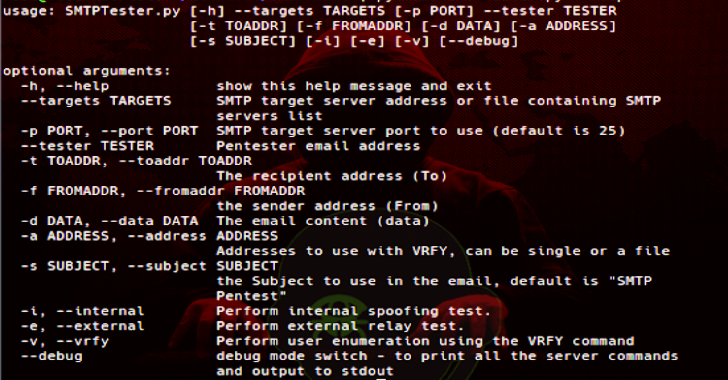
SMTPTester : Small Python3 Tool To Check Common Vulnerabilities In SMTP...
SMTPTester is a python3 tool to test SMTP server for 3 common vulnerabilities:
Spoofing - The ability to send a mail on behalf of an...
© kalilinuxtutorials.com 2025