APPLICATIONS
HOT NEWS
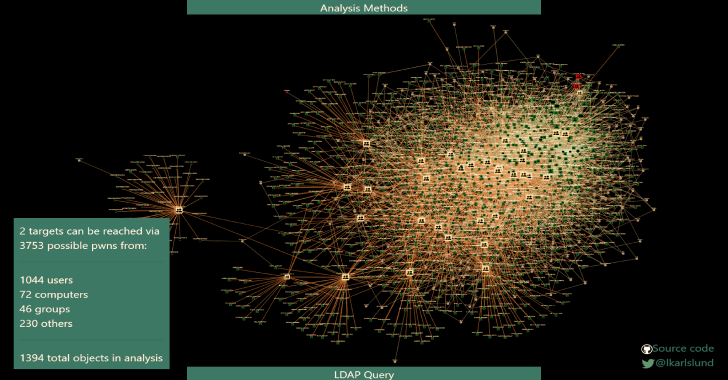
adalanche : Active Directory ACL Visualizer and Explorer
adalanche is a Active Directory security is notoriously difficult. Small organizations generally have no idea what they're doing, and way too many people are...
© kalilinuxtutorials.com 2025