APPLICATIONS
HOT NEWS
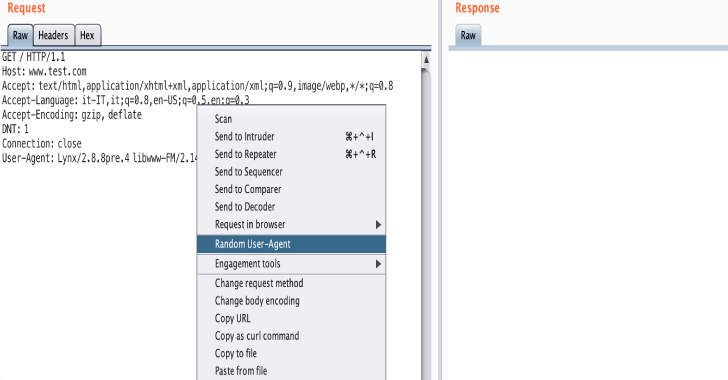
Burp Suite Extension For Generate A Random User Agents
A Burp Suite extension to help pentesters to generate a random user-agent. This extension has been developed by M'hamed (@m4ll0k) Outaadi.
Installation
Download...
© kalilinuxtutorials.com 2025