APPLICATIONS
HOT NEWS
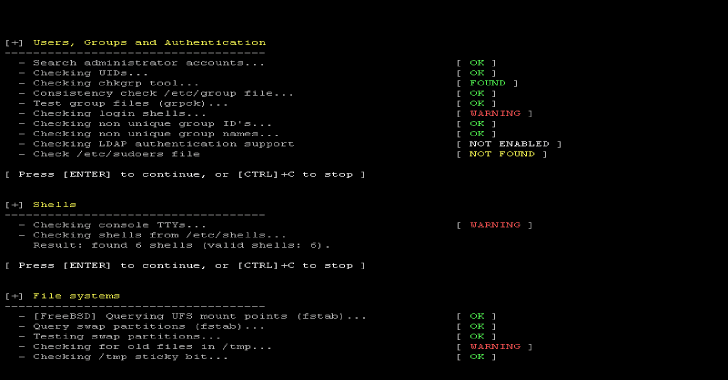
Lynis : Security Auditing Tool for Unix/Linux Systems
Lynis is a security auditing tool for UNIX derivatives like Linux, macOS, BSD, Solaris, AIX, and others. It performs an in-depth security scan. Software...
© kalilinuxtutorials.com 2025