APPLICATIONS
HOT NEWS
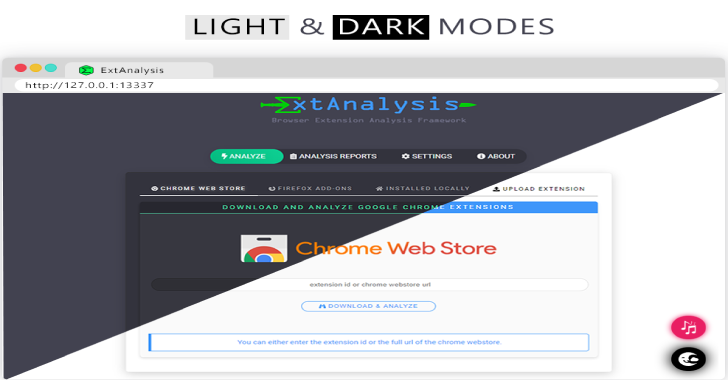
ExtAnalysis : Browser Extension Analysis Framework
ExtAnalysis is a browser extension analysis framework. Installing it is simple! It runs on python3, so make sure python3 and python3-pip are installed.
What Can...
© kalilinuxtutorials.com 2025





.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)