APPLICATIONS
HOT NEWS
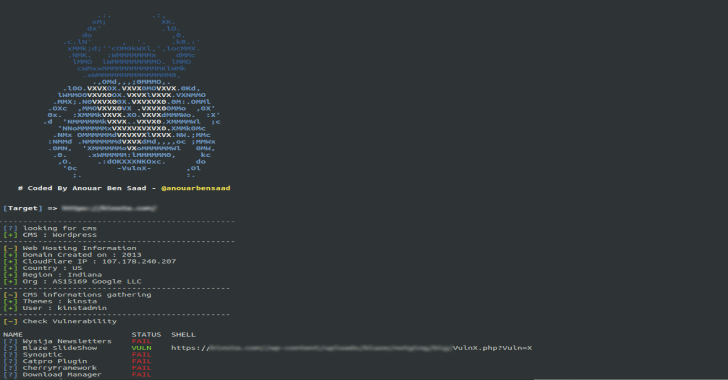
Vulnx : Auto Shell Injector That Detect Vulnerabilities In Multiple Types...
Vulnx is An Intelligent Bot Auto Shell Injector that detects vulnerabilities in multiple types of Cms, fast cms detection,information gathering and vulnerabilities Scanning of...
© kalilinuxtutorials.com 2025





.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
%20(1).png)
.webp)
.webp)