APPLICATIONS
HOT NEWS
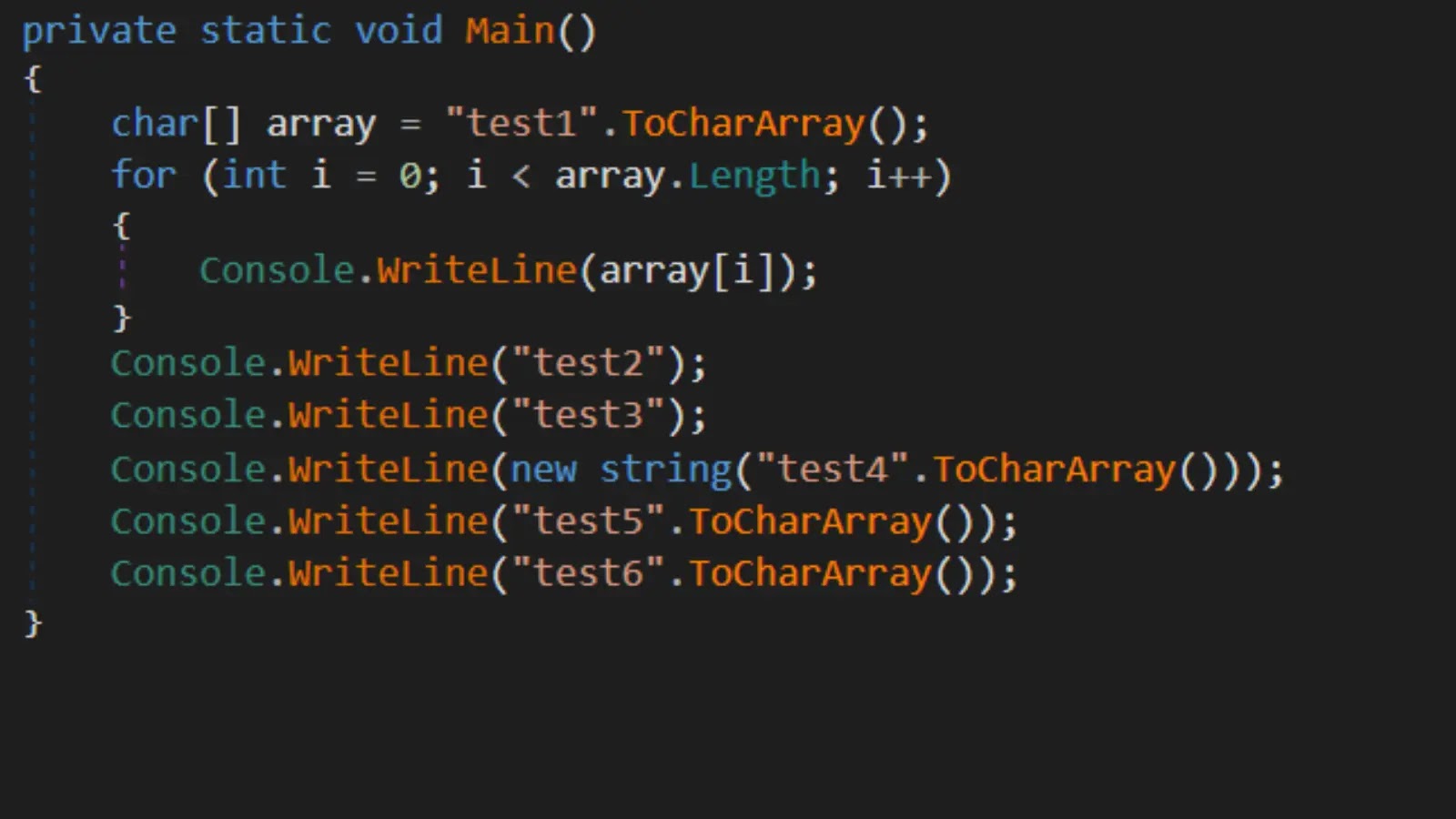
Blindsight : Advanced Techniques In Red Teaming And LSASS Memory Exploitation
Blindsight is a red teaming tool designed to dump LSASS (Local Security Authority Subsystem Service) memory on Windows systems, bypassing basic countermeasures.
It utilizes...
© kalilinuxtutorials.com 2025