APPLICATIONS
HOT NEWS
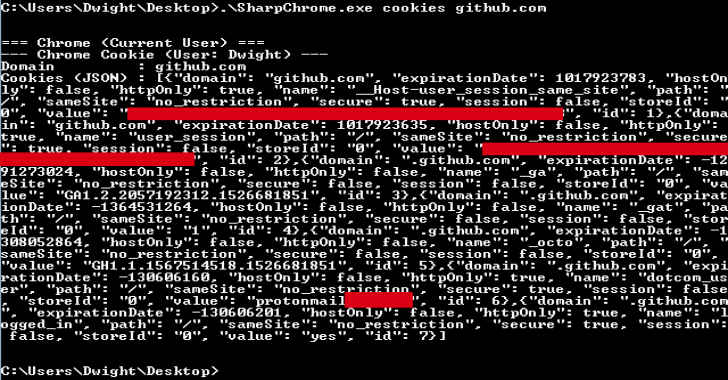
SharpChromium : .NET 4.0 CLR Project To Retrieve Chromium Data, Such...
SharpChromium is a .NET 4.0+ CLR project to retrieve data from Google Chrome, Microsoft Edge, and Microsoft Edge Beta. Currently, it can extract:
Cookies (in...
© kalilinuxtutorials.com 2025









.webp)