APPLICATIONS
HOT NEWS
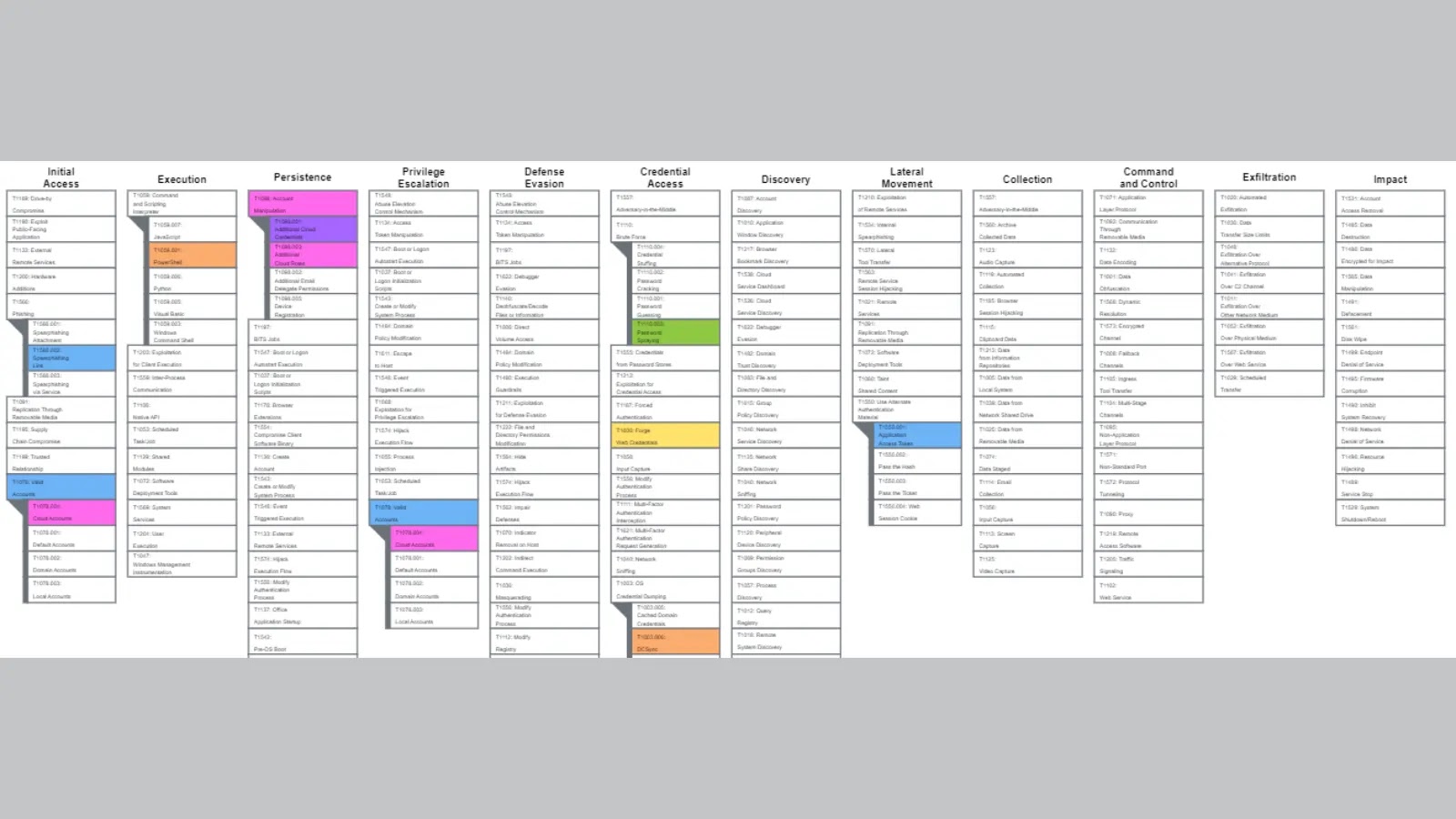
Azure AD Attack & Defense Playbook
This publication is a collection of various common attack scenarios on Azure Active Directory and how they can be mitigated or detected.
All of...
© kalilinuxtutorials.com 2025





.png)