APPLICATIONS
HOT NEWS
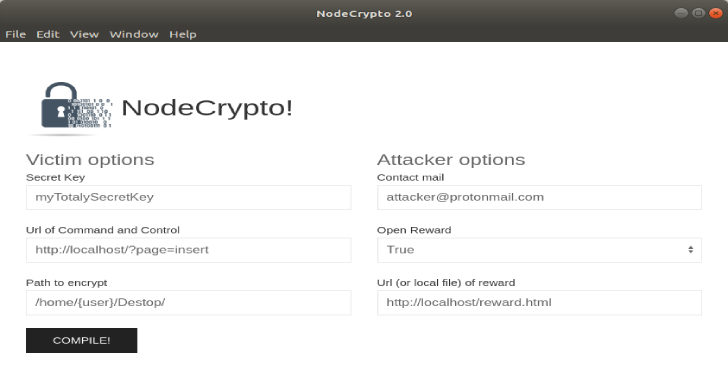
NodeCrypto : Linux Ransomware Written In NodeJs
NodeCrypto is a Linux Ransomware written in NodeJs that encrypt predefined files. This project was created for educational purposes, you are the sole responsible...
© kalilinuxtutorials.com 2025





.png)