APPLICATIONS
HOT NEWS
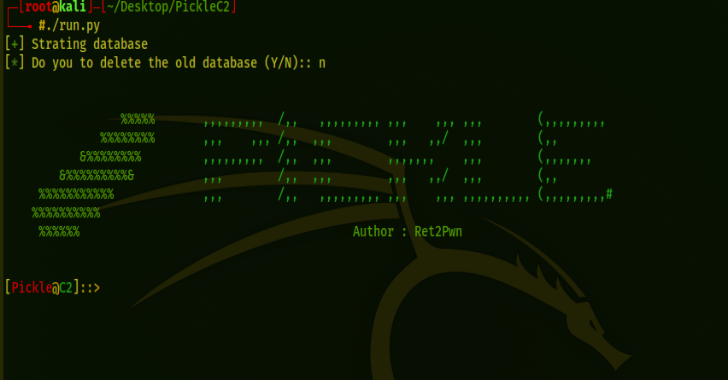
EGO Vulnerability Scanner – Revolutionizing Cybersecurity With Advanced Scanning Capabilities
EGO is a vulnerability scanner developed by chickenpwny at PolitoInc. It was created to provide a platform for hackers to store multiple projects in...
© kalilinuxtutorials.com 2025







.webp)