APPLICATIONS
HOT NEWS
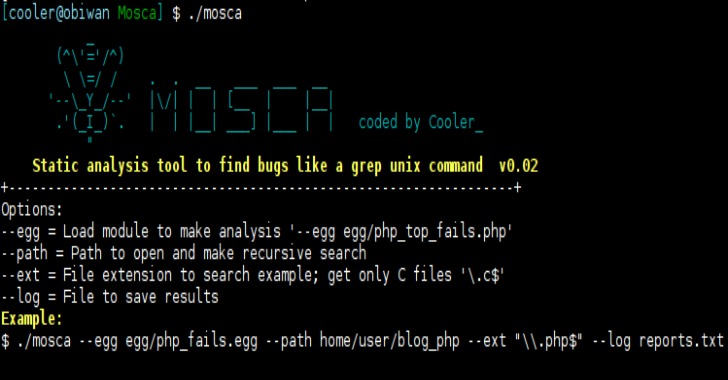
Mosca : Manual Search Tool To Find Bugs Like A Grep...
Mosca is a manual analysis tool to find bugs like a grep unix command and since it is not dynamic the uses static code...
© kalilinuxtutorials.com 2025