APPLICATIONS
HOT NEWS
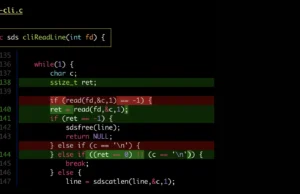
Delta : A Powerful Syntax-Highlighting Pager For Git And Command-Line Workflows
Delta is a powerful syntax-highlighting pager designed to enhance the experience of working with Git, diff, and grep outputs in the command line.
Built...
© kalilinuxtutorials.com 2025