APPLICATIONS
HOT NEWS
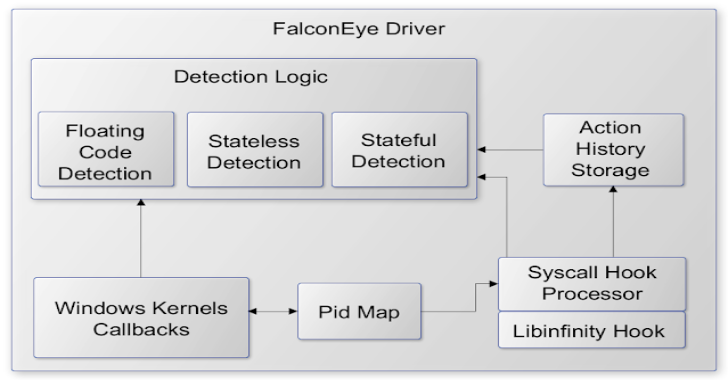
FalconEye : Real-time detection software for Windows process injections
FalconEye is a windows endpoint detection software for real-time process injections. It is a kernel-mode driver that aims to catch process injections as they...
© kalilinuxtutorials.com 2025