APPLICATIONS
HOT NEWS
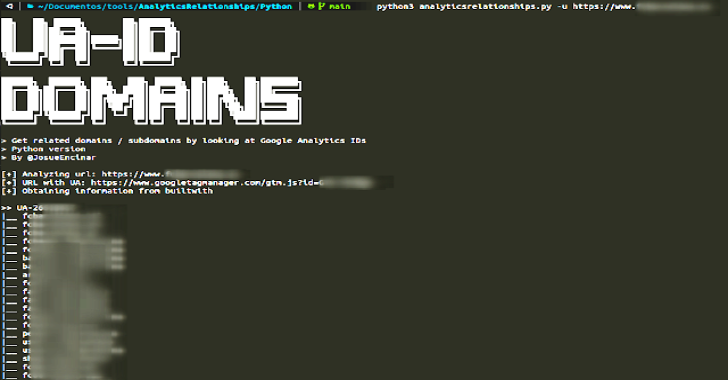
AnalyticsRelationships : Get Related Domains / Subdomains By Looking At Google...
AnalyticsRelationships is a tool to Get Related Domains / Subdomains By Looking At Google Analytics IDs.
██╗ ██╗ █████╗ ...
© kalilinuxtutorials.com 2025