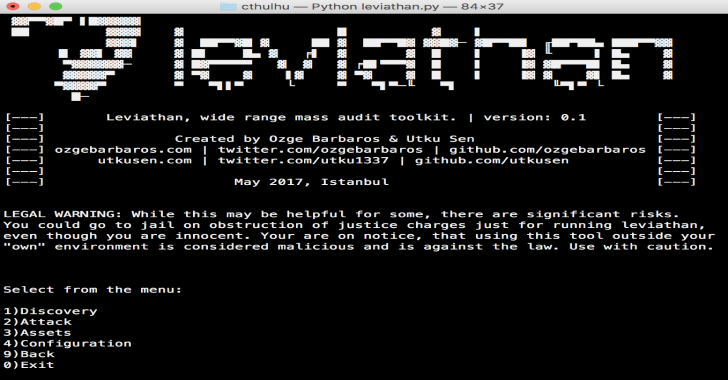
APPLICATIONS
HOT NEWS
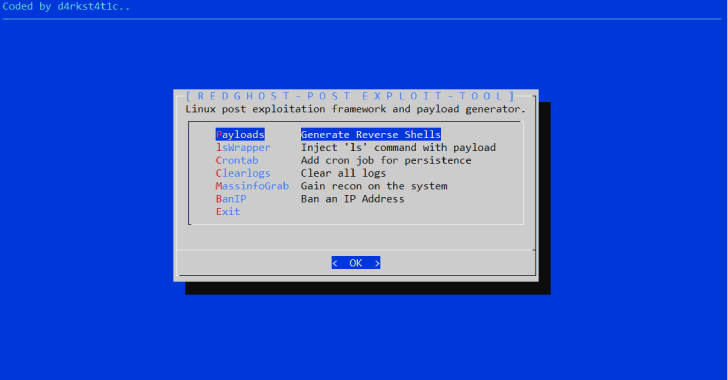
BackBox : Tool To Perform Penetration Tests & Security Assessments
BackBox is a Linux distribution based on Ubuntu. It has been developed to perform penetration tests and security assessments.
Designed to be fast, easy...
© kalilinuxtutorials.com 2025