BadZure is a PowerShell script that uses the Microsoft Graph SDK to set up Azure Active Directory tenants. It fills them with different entities and makes common security mistakes to make tenants that are easy to attack and have multiple entry points.
BadZure automates the process of creating users, groups, application registrations, service principals, and administrative units, among other things.
It gives Azure AD roles, Graph permissions, and application ownership privileges to randomly chosen security principals to mimic common security misconfigurations in real environments.
This lets it create new attack paths. In line with the “Assume Breach” principle, BadZure gives users two ways to gain initial access to the vulnerable tenants it makes. This simulates account takeover scenarios.
BadZure’s main benefit is that it can quickly fill and clean up existing Azure AD tenants with randomly generated vulnerable configurations and pre-configured initial access.
This makes it easier for both the red team (attack simulation) and the blue team (detection development) to try out new ideas. It is made for security professionals who want to learn more about and explore Azure AD security.
Goals and Use Cases
BadZure was first made for a class at X33fcon 2023 called Azure AD Battle School: Hands-on Attack and Defense.
When BadZure is added to an Azure AD tenant, red and blue teams can also:
- Try out popular ways and tools to attack Azure AD (for ideas, see the Azure AD Attack and Defense Playbook).
- Set up quickly Azure AD lab users that have been set up wrong.
- Get information about attacks so you can build, test, and improve detection controls.
- Purple team routines should be done in a safe place.
- Help set up hands-on security training for Azure AD.
- Attack Paths Host changeable Azure AD Capture the Flag (CTF) events.
Attack Paths
Initial Access
BadZure makes it easier to log in for the first time by modeling account takeover methods like password attacks and token theft. It accomplishes this by giving the principal JWT access tokens or assigning a password (which the user can choose or generate randomly).
BadZure also instantly makes a file called “users.txt” that lists the usernames of the new accounts. This is done to support testing methods like “password spraying.” Users can put themselves in the shoes of an attacker who is going after an Azure AD tenant by using the passwords or tokens that are given out in the output.
Privilege Escalation
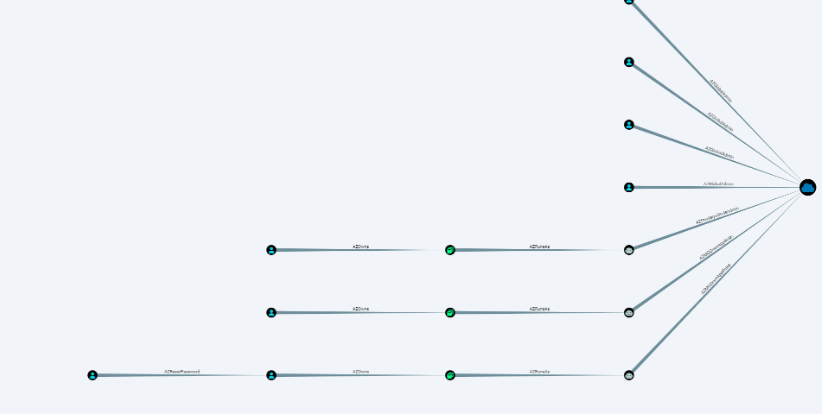
BadZure makes three attack vectors for gaining more privileges by simulating service principal abuse situations. It does this by making sure that Azure AD roles, Graph rights, and application ownerships cause misconfigurations. Below is a BloodHound-made image that shows the attack paths that BadZure makes.
Demo
You can learn more and download this tool here






.webp)

.jpg)




