What is C2IntelFeeds?
C2IntelFeeds is an open-source intelligence project that provides real-time Command and Control (C2) infrastructure data. Using data from Censys and custom detection signatures, it identifies and tracks malicious C2 servers, domains, and IP addresses that threat actors use for cyberattacks.
By leveraging these feeds, security teams can detect threats earlier, improve incident response, and block malicious infrastructure before it can be used against them.
Key Features
- Live C2 IP Feeds – Active IPs hosting malicious C2 services (excluding CDN/frontends).
- Domain Feeds – Extracted C2 domain names, including those used in domain fronting attacks.
- Filtered Feeds – Cleaned datasets excluding popular abused domains like Microsoft, Google, and Apple.
- URL & IP Enriched Feeds – Includes exact C2 endpoints for deeper analysis.
- Unverified Feeds – Potential C2 servers that require manual verification.
- Additional Data – VPN node lists and detailed Cobalt Strike configurations for advanced threat hunting.
Why It’s Valuable for Cybersecurity
Tracking C2 infrastructure is critical for:
- Threat Hunting – Identifying indicators of compromise (IOCs) in your environment.
- Penetration Testing – Simulating real-world attacks using current threat actor infrastructure.
- SOC Operations – Blocking malicious IPs and domains before they become active threats.
- Incident Response – Quickly correlating alerts with known malicious infrastructure.
Supported C2 Frameworks
C2IntelFeeds tracks multiple popular and dangerous C2 frameworks, including:
- Cobalt Strike
- Sliver
- Brute Ratel C4
- Mythic
- Havoc
- Pupy RAT
- AsyncRAT
- NetSupport Manager RAT
…and dozens more, including emerging malware like Pikabot, Meduza Stealer, and StealC v2.
Getting Started
You can access ready-to-use feeds here:
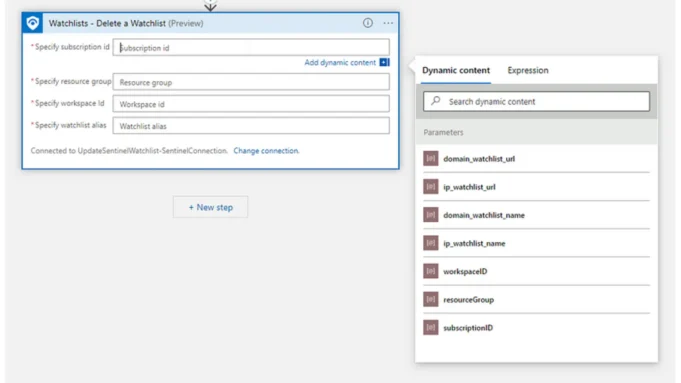
These feeds can be integrated directly into your SIEM, firewall, or EDR solutions for automated blocking and monitoring.
Conclusion
C2IntelFeeds is a must-have resource for cybersecurity professionals, SOC teams, and threat hunters who want to proactively defend against C2-based attacks. By integrating these feeds into your security stack, you can detect threats faster, block malicious actors before they strike, and keep your organization one step ahead. Mitigate malicious activities, ultimately strengthening their cybersecurity posture.





.jpg)