DejaVU is a open source deception framework. Deception techniques if deployed well can be very effective for organizations to improve network defense and can be a useful arsenal for blue teams to detect attacks at very early stage of cyber kill chain. But the challenge we have seen is deploying, managing and administering decoys across large networks is still not easy and becomes complex for defenders to manage this over time. Although there are a lot of commercial tools in this space, we haven’t come across open source tools which can achieve this. Credits to Bhadresh Patel and Harish Ramadoss.
Video demo for tool is published here
Also Read Delta – SDN Security Evaluation & Penetration Testing Framework
DejaVU Usage Guide
Initial Setup
- Quick setup video guide – https://youtu.be/NOuEGa0241U
- Command-line interface credentials – administrator:changepassword
Add Server Decoy
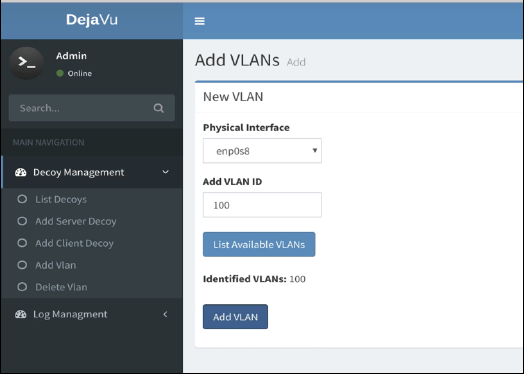
- To add a decoy, we first need to add a VLAN on which we want to later deploy Decoys.
- Select Decoy Management -> Add VLAN
- Enter the VLAN ID. Use the “List Available VLANs” option to list the VLANs tagged on the interface.
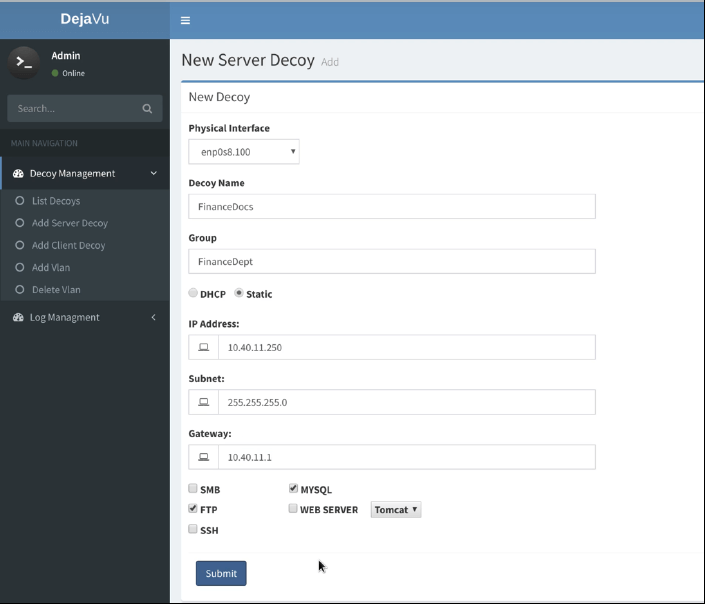
- To add server decoy :
- Select Decoy Management ->Add Server Decoy
- Provide the details for new decoy as shown below. Select the services (SMB/FTP/MySQL/FTP/Web Server/SSH) to be deployed, use dynamic or provide a static IP address.
- Let’s do some port scan’s + Auth attempts from attacker machine on server VLAN and analyze the alerts.
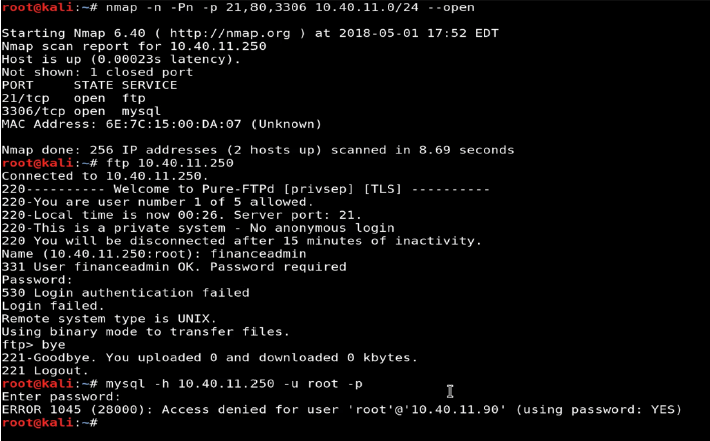
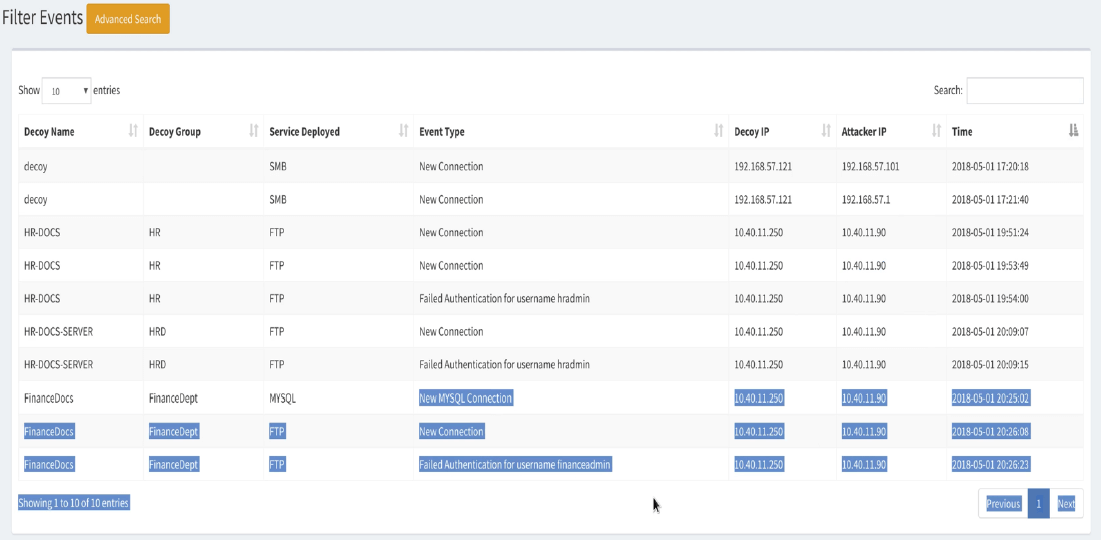
- View the alerts triggered when the attacker scanned our decoy and tried to authenticate.
- Select Log Management -> List Events
Add Client Decoy
- To add Client Decoy
- Select Decoy Management ->Add Client Decoy
- Provide the details for new decoy as shown below. It’s recommended to place the client decoy on user VLANs to detect responder/LLMNR attacks.

- Let’s run responder from attacker machine on end user VLAN and analyze the alerts.
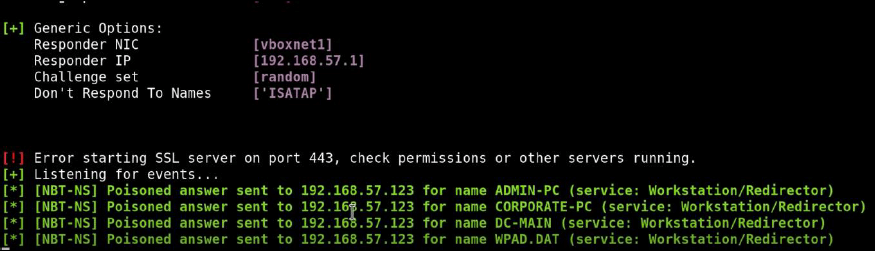
- View the alerts triggered when the attacker scanned our decoy and tried to authenticated.
- Log management -> List Events

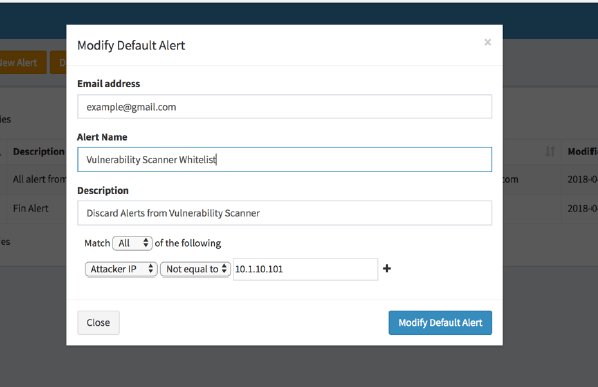
Filter Alerts
- Alerts can be configured based on various parameters. Example – Don’t send alerts from IP – 10.1.10.101. If certain IP’s like in-house vulnerability scanner, SCCM etc. needs to be whitelisted.