To find out the arbitration IDs and the corresponding message data and positional bytes for all the actions in GearGoat using CaringCaribou.
Solution
Step 0: To install Caring Caribou:
- Clone the repository and run the installation file:
git clone https://github.com/CaringCaribou/caringcaribou.git
cd caringcaribou/
sudo python3 setup.py installReturn back to the previous location and run the following:
cd ..
printf "[default]\ninterface = socketcan\nchannel = vcan0" > $HOME/.canrcMore info here:- CaringCaribou
Step 1: The GearGoat setup will look something like this with terminal in background and the GearGoat window marked on top.
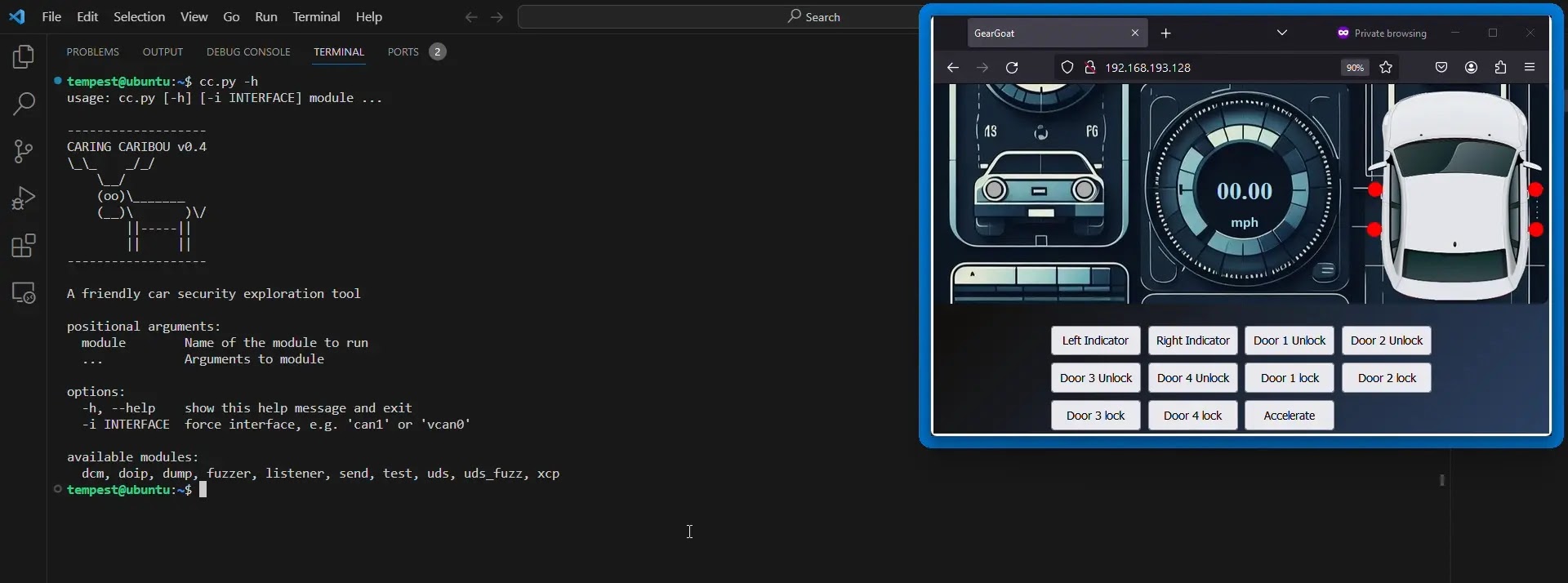
Step 2: We will explore the reverse engineering capabilities of “CaringCaribou” using “GearGoat”. We will try to figure out the Arbitration IDs of the actions we performed in the simulator.
First we will scan for unique Arbitration IDs in the network using the “listener” module.
Command:
cc.py listener -hCommand:
cc.py listener -rFor more information click here.