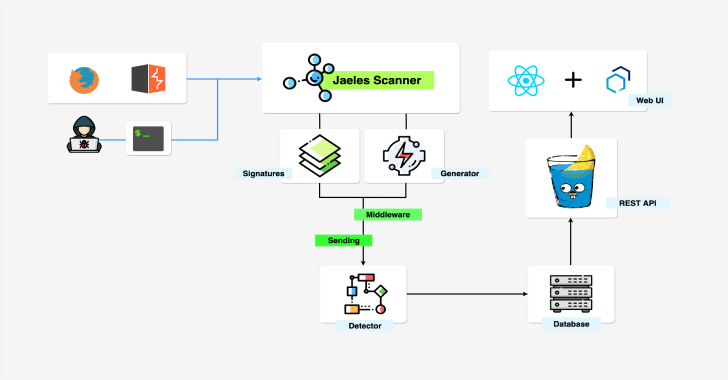
Jaeles is a powerful, flexible and easily extensible framework written in Go for building your own Web Application Scanner.
Installation
Download precompiled version here.
If you have a Go environment, make sure you have Go >= 1.13 with Go Modules enable and run the following command.
GO111MODULE=on go get github.com/jaeles-project/jaeles
Please visit the Official Documention for more details.
Note: Checkout Signatures Repo for install signature.
Usage
#Scan Usage example:
jaeles scan -s -u
jaeles scan -c 50 -s -U -L
jaeles scan -c 50 -s -U
jaeles scan -c 50 -s -U -p ‘dest=xxx.burpcollaborator.net’
jaeles scan -c 50 -s -U -f ‘noti_slack “{{.vulnInfo}}”‘
jaeles scan -v -c 50 -s -U list_target.txt -o /tmp/output
jaeles scan -s -s -u http://example.com
jaeles scan -G -s -s -x -u http://example.com
cat list_target.txt | jaeles scan -c 100 -s
#Examples:
jaeles scan -s ‘jira’ -s ‘ruby’ -u target.com
jaeles scan -c 50 -s ‘java’ -x ‘tomcat’ -U list_of_urls.txt
jaeles scan -G -c 50 -s ‘/tmp/custom-signature/.‘ -U list_of_urls.txt jaeles scan -v -s ‘~/my-signatures/products/wordpress/.‘ -u ‘https://wp.example.com’ -p ‘root=[[.URL]]’
cat urls.txt | grep ‘interesting’ | jaeles scan -L 5 -c 50 -s ‘fuzz/.*’ -U list_of_urls.txt –proxy http://127.0.0.1:8080
Also Read – Evilreg : Reverse Shell Using Windows Registry Files (.reg)
Showcases
HTML Report Summary

Burp Integration

Planned Features
- Adding more signatures.
- Adding more input sources.
- Adding more APIs to get access to more properties of the request.
- Adding proxy plugins to directly receive input from browser of http client.
Adding passive signature for passive checking each request.- Adding more action on Web UI.
- Integrate with many other tools.