Home Search
vulnerable - search results
If you're not happy with the results, please do another search
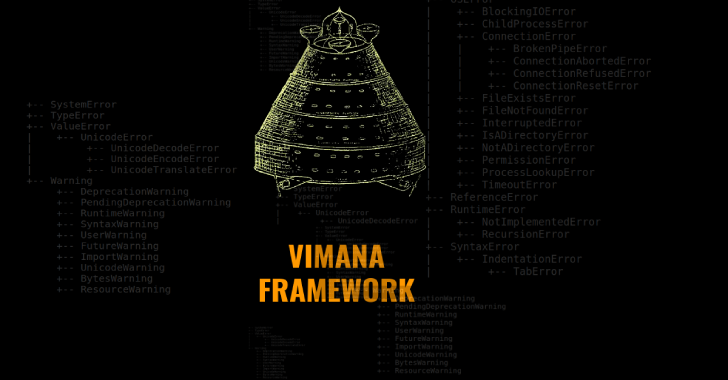
Vimana : An Experimental Security Framework That Aims To Provide Resources For Auditing Python...
Vimana is a modular security framework designed to audit Python web applications.
Framework Structure
The base of the Vimana is composed of crawlers focused on frameworks...
Metabadger : Prevent SSRF Attacks On AWS EC2 Via Automated Upgrades To The More...
Metabadger Prevent SSRF attacks on AWS EC2 via automated upgrades to the more secure Instance Metadata Service v2 (IMDSv2).
Metabadger
Purpose and functionality
Diagnose and evaluate your...
DorkScout : Golang Tool To Automate Google Dork Scan Against The Entiere Internet Or...
DorkScout is a tool to automate the finding of vulnerable applications or secret files around the internet throught google searches, dorkscout first starts by...
ImpulsiveDLLHijack : C# Based Tool Which Automates The Process Of Discovering And Exploiting DLL...
ImpulsiveDLLHijack is a C# based tool which automates the process of discovering and exploiting DLL Hijacks in target binaries. The Hijacked paths discovered can...
Domain-Protect : Protect Against Subdomain Takeover
Domain-Protect scans Amazon Route53 across an AWS Organization for domain records vulnerable to takeovervulnerable domains in Google Cloud DNS can be detected by Domain Protect...
JSPanda : Client-Side Prototype Pollution Vulnerability Scanner
JSpanda is client-side prototype pollution vulnerability scanner. It has two key features, scanning vulnerability the supplied URLs and analyzing the JavaScript libraries' source code.
However,...
Certify : Active Directory Certificate Abuse
Certify is a C# tool to enumerate and abuse misconfigurations in Active Directory Certificate Services (AD CS).
Usage
C:Tools>Certify.exe_ _ _ / | | | ()/...
Concealed Position : Bring Your Own Print Driver Privilege Escalation Tool
Concealed Position is a local privilege escalation attack against Windows using the concept of "Bring Your Own Vulnerability". Specifically, Concealed Position (CP) uses the as...
Plution : Prototype Pollution Scanner Using Headless Chrome
Plution is a convenient way to scan at scale for pages that are vulnerable to client side prototype pollution via a URL payload. In...
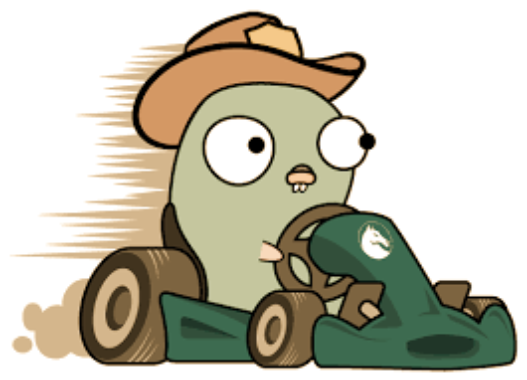
Gokart : A Static Analysis Tool For Securing Go Code
GoKart is a static analysis tool for Go that finds vulnerabilities using the SSA (single static assignment) form of Go source code. It is...