PEpper is an open source tool to perform malware static analysis on Portable Executable. Following are some of the features supported by the tool;
- Suspicious entropy ratio
- Suspicious name ratio
- Suspicious code size
- Suspicious debugging time-stamp
- Number of export
- Number of anti-debugging calls
- Number of virtual-machine detection calls
- Number of suspicious API calls
- Number of suspicious strings
- Number of YARA rules matches
- Number of URL found
- Number of IP found
- Cookie on the stack (GS) support
- Control Flow Guard (CFG) support
- Data Execution Prevention (DEP) support
- Address Space Layout Randomization (ASLR) support
- Structured Exception Handling (SEH) support
- Thread Local Storage (TLS) support
- Presence of manifest
- Presence of version
- Presence of digital certificate
- Packer detection
- VirusTotal database detection
- Import hash
Installation
eva@paradise:~$ git clone https://github.com/Th3Hurrican3/PEpper/ eva@paradise:~$ cd PEpper
eva@paradise:~$ pip3 install -r requirements.txt
eva@paradise:~$ python3 pepper.py ./malware_dir
CSV Output
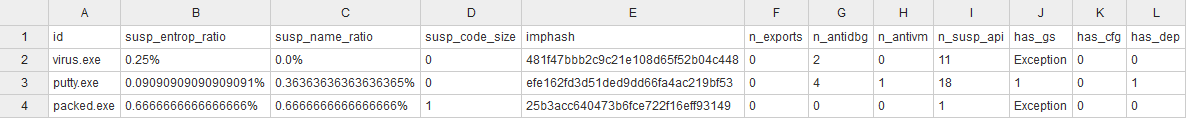
and more columns..
Also Read – PwnedOrNot : OSINT Tool To Find Passwords For Compromised Email Addresses
Notes
- Can be run on single or multiple PE (placed inside a directory)
- Output will be saved (in the same directory of pepper.py) as output.csv
- To use VirusTotal scan, add your private key in the module called “virustotal.py” (Internet connection required)
Screenshots















