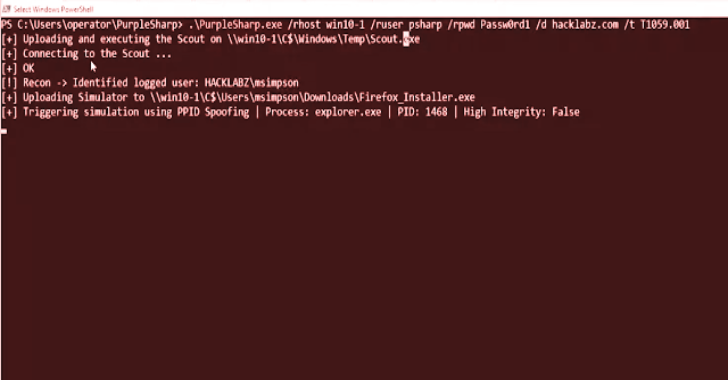
PurpleSharp is an open source adversary simulation tool written in C# that executes adversary techniques within Windows Active Directory environments.
The resulting telemetry can be leveraged to measure and improve the efficacy of a detection engineering program.
PurpleSharp leverages the MITRE ATT&CK Framework and executes different techniques across the attack life cycle: execution, persistence, privilege escalation, credential access, lateral movement, etc. It currently supports 37 unique ATT&CK techniques.
PurpleSharp was first presented at Derbycon IX on September 2019.
An updated version was released on August 6th 2020 as part of BlackHat Arsenal 2020. If you want to jump straight to the demos: Demo 1 and Demo 2.
Goals / Use Cases
The attack telemetry produced by simulating techniques with PurpleSharp aids detection teams in:
- Building new detecttion analytics
- Testing existing detection analytics
- Validating detection resiliency
- Identifying gaps in visibility
- Identifing issues with event logging pipeline
Quick Start Guide
- PurpleSharp can be built with Visual Studio Community 2019 or 2020.
- .NET Framework 4.5 is required.
Credit: Mauricio Velazco – @mvelazco