The Hawkeye Scanner CLI is a project security, vulnerability and general risk highlighting tool. It is meant to be integrated into your pre-commit hooks and your pipelines.
Running & Configuring the Scanner
The Hawkeye scanner-cli assumes that your directory structure is such that it keeps the toolchain’s files on top level. Roughly, this is what it boils down to:
- Node.js projects have a
package.jsonon top level - Ruby projects will have a
Gemfileon top level - Python projects will have a
requirements.txton top level - PHP projects will have a
composer.lockon top level - Java projects will have a
build(gradle) ortarget(maven) folder, and include.javaand.jarfiles
This is not exhaustive as sometimes tools require further files to exist. To understand how the modules decide whether they can handle a project.
Also Read : Twifo CLI:Get Twitter User Information 2019
The docker image is hands-down the easiest way to the scanner. Please note that your project root (e.g. $PWD) needs to be mounted to /target.
docker run –rm -v $PWD:/target hawkeyesec/scanner-cli
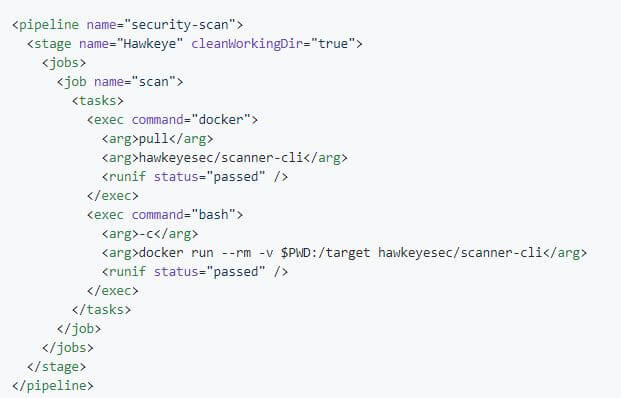
The docker build is also the recommended way to run the scanner in your CI pipelines. This is an example of running Hawkeye against one of your projects in GoCD:
npm
You can install and run hawkeye in a Node.js project via
npm install –save-dev @hawkeyesec/scanner-cli
npx hawkeye scan
This method is recommended in a Node.js project, where the other toolchains (e.g. python, ruby) are not required.
With this method, it is also recommended to invoke the scanner in a git pre-commit hook (e.g. via the pre-commit package) to fail the commit if issues are found.
Configuration Files (recommended)
You can configure the scanner via .hawkeyerc and .hawkeyeignore files in your project root.
The .hawkeyerc file is a JSON file that allows you to configure …
- the modules to run,
- the writers to use, and
- the failure threshold
{
“all”: true|false,
“staged”: true|false,
“modules”: [“files-ccnumber”, “java-owasp”, “java-find-secbugs”],
“sumo”: “http://your.sumologic.foobar/collector”,
“http”: “http://your.logger.foobar/collector”,
“json”: “log/results.json”,
“failOn”: “low”|”medium”|”high”|”critical”,
“showCode”: true|false
}
The .hawkeyeignore file is a collection of regular expressions matching paths and module error codes to exclude from the scan, and is equivalent to using the --exclude flag. Lines starting with # are regarded as comments.
Please note that any special charaters reserved in regular expressions (-[]{}()*+?.,^$|#\s) need to be escaped when used as a literal!
Please also note that the module error codes are usually not shown, since they are not primarily relevant for the user.
If you want to exclude a certain false positive, you can display the module error codes with the flag --show-code or the showCodeproperty in the .hawkeyerc.
^test/
this is a comment
^README.md
How it works
Hawkeye is designed to be extensible by adding modules and writers.
- Add modules in the modules folder.
- Add writers in the writers folder.
Modules are basically little bits of code that either implement their own logic, or wrap a third party tool and standardise the output. They only run if the required criteria are met. For example: The npm outdated module would only run if a package.json is detected in the scan target – as a result, you don’t need to tell Hawkeye what type of project you are scanning.
- files-ccnumber: Scans for suspicious file contents that are likely to contain credit card numbers
- files-contents: Scans for suspicious file contents that are likely to contain secrets
- files-entropy: Scans files for strings with high entropy that are likely to contain passwords. Entropy scanning is disabled by default because of the high number of false positives. It is useful to scan codebases every now and then for keys, in which case please run it please using the
-m files-entropyswitch. - files-secrets: Scans for suspicious filenames that are likely to contain secrets
- java-find-secbugs: Finds common security issues in Java code with findsecbugs
- java-owasp: Scans Java projects for gradle/maven dependencies with known vulnerabilities with the OWASP dependency checker
- node-crossenv: Scans node projects for known malicious crossenv dependencies
- node-npmaudit: Checks node projects for dependencies with known vulnerabilities with npm audit
- node-npmoutdated: Checks node projects for outdated npm modules with npm outdated
- node-yarnaudit: Checks yarn projects for dependencies with known vulnerabilities with yarn audit
- node-yarnoutdated: Checks node projects for outdated yarn modules with yarn outdated
- php-security-checker: Checks whether the composer.lock contains dependencies with known vulnerabilities using security-checker
- python-bandit: Scans for common security issues in Python code with bandit.
- python-piprot: Scans python dependencies for out of date packages with piprot
- python-safety: Checks python dependencies for known security vulnerabilities with the safety tool.
- ruby-brakeman: Statically analyzes Rails code for security issues with Brakeman.
- ruby-bundler-scan: Scan for Ruby gems with known vulnerabilities using bundler
If you have an idea for a module, please feel free open a feature request in the issues section.
If you have a bit of time left, please consider sending us a pull request. To see modules work, please head over to the modules folder to find how things are working.











.png)