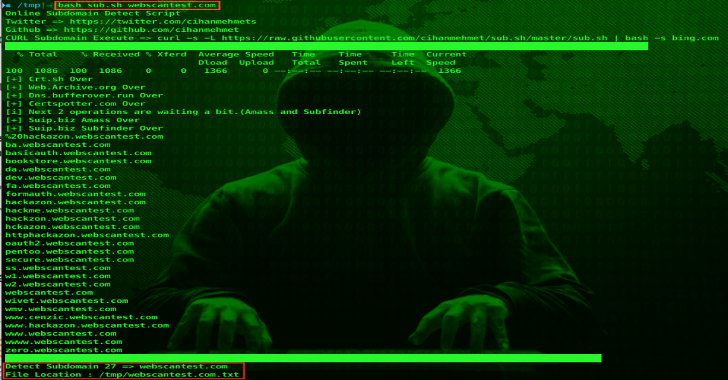
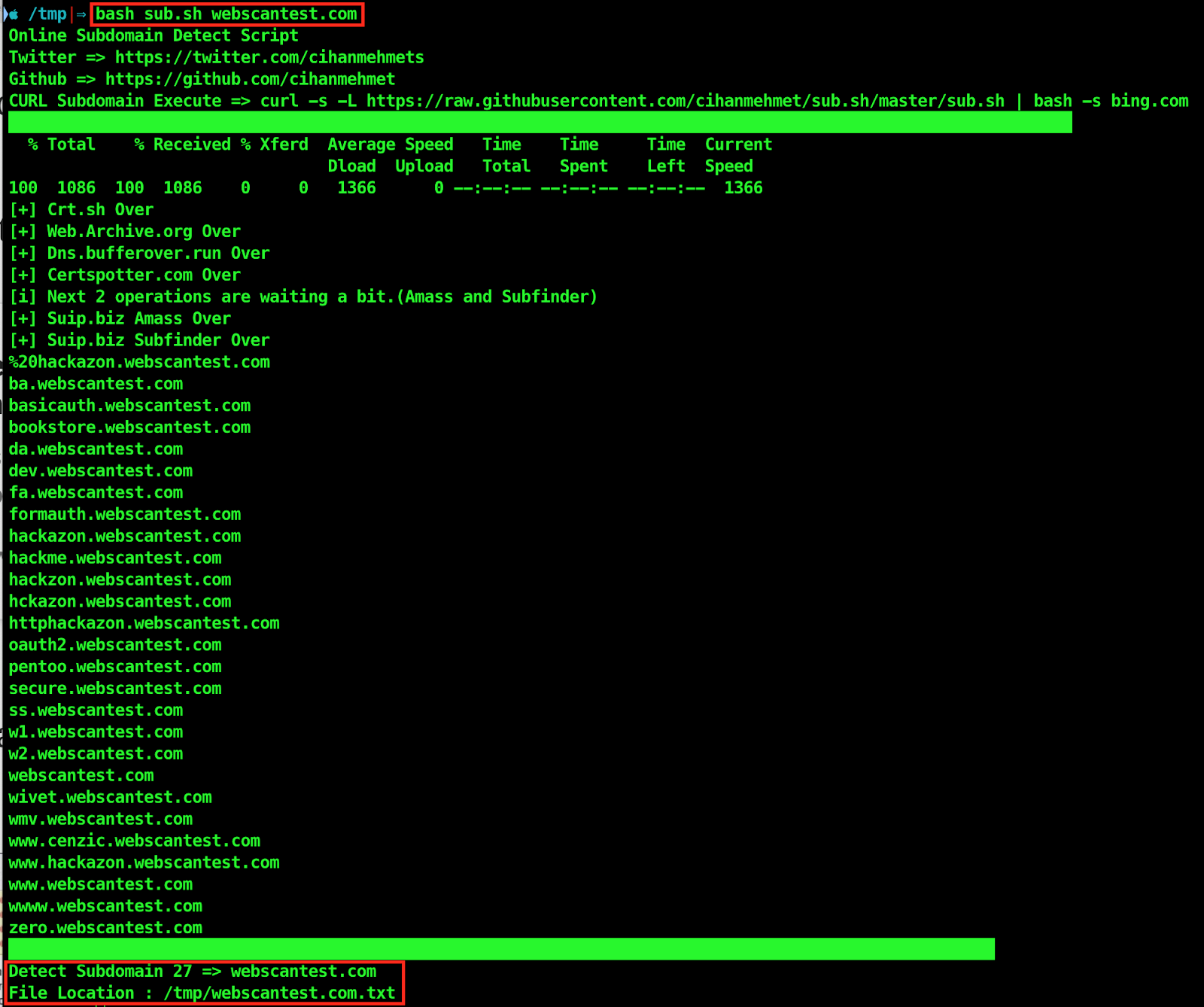
Sub.sh is a script to detect subdomain online. So let us have a look on it usage.
Script
bash sub.sh webscantest.com
./sub.sh webscantest.com
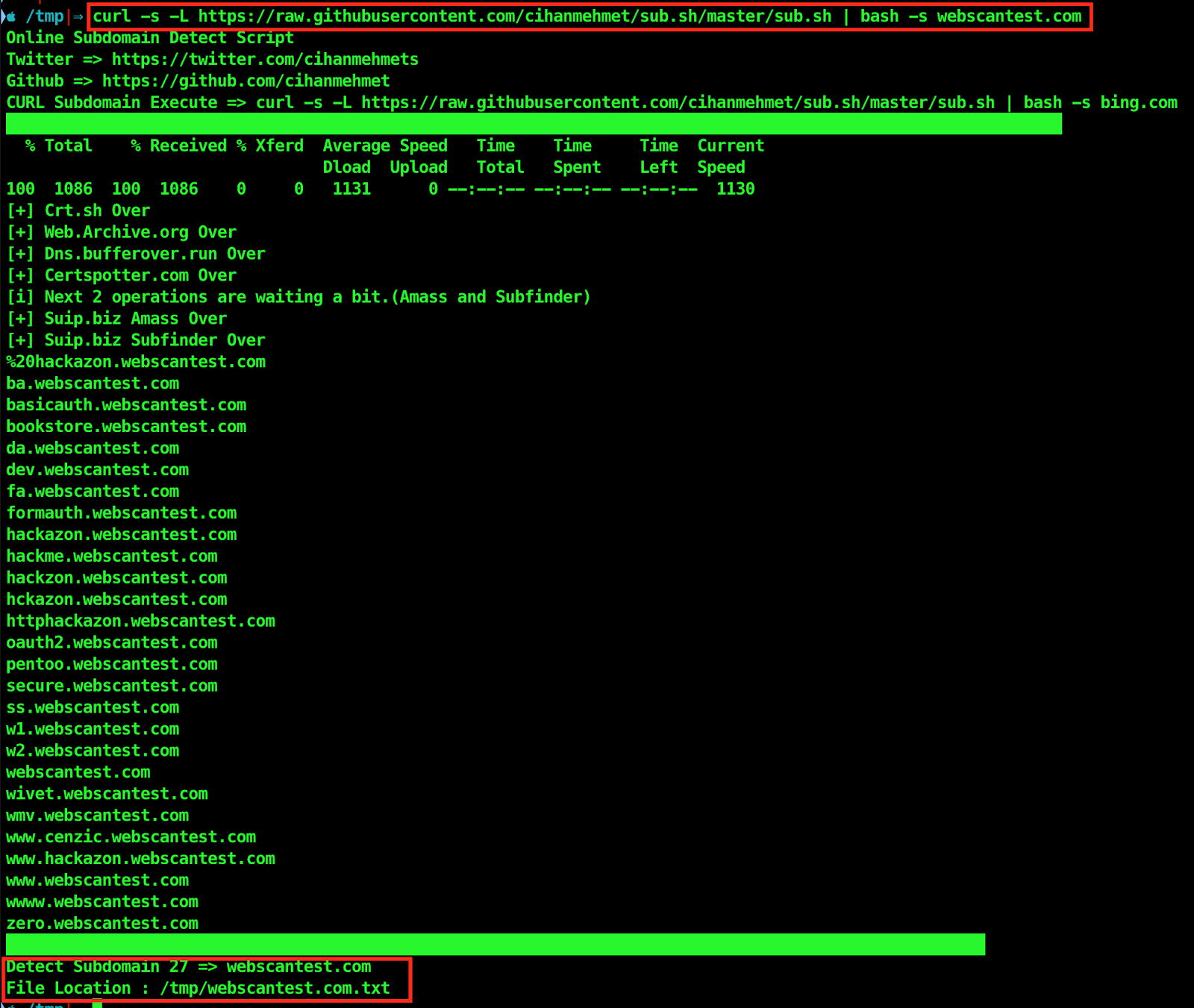
Curl
curl -s -L https://raw.githubusercontent.com/cihanmehmet/sub.sh/master/sub.sh | bash -s webscantest.com
Also Read – Re-composer : Randomly Changes Win32/64 PE Files For ‘Safer’ Uploading To Malware & Sandbox Sites
Subdomain Alive Check
bash sub_alive.sh bing.com
curl -s -L https://raw.githubusercontent.com/cihanmehmet/sub.sh/master/sub_alive.sh | bash -s bing.com”
Fping Required

Nmap -sn (No port scan) scan live IP detection script
fping -f ip.txt
Usage bash nmap_sn.sh ip.txt

#!/bin/bash
nmap -sn -iL $1 |grep “Nmap scan report for”|grep -Eo “(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?).(25[0-5]|2[0-4][0-9]|[01]?[0-9][0-9]?)”|sort -u |tee $1.txt
echo “Detect IP $(wc -l $1.txt|awk ‘{ print $1 }’ )” “=> result_${1}” “saved”
echo “File Location : “$(pwd)/”result_$1”
Sample usage
Usage 1(fping)fping dart
cat domains.txt | dnsgen – |fping|grep “alive”|cut -d ” ” -f1>resolvers.txt
Usage 2(httprobe ) dart
cat domains.txt | dnsgen – |httprobe|cut -d “/” -f3|sort -u |tee resolvers.txt