APPLICATIONS
HOT NEWS
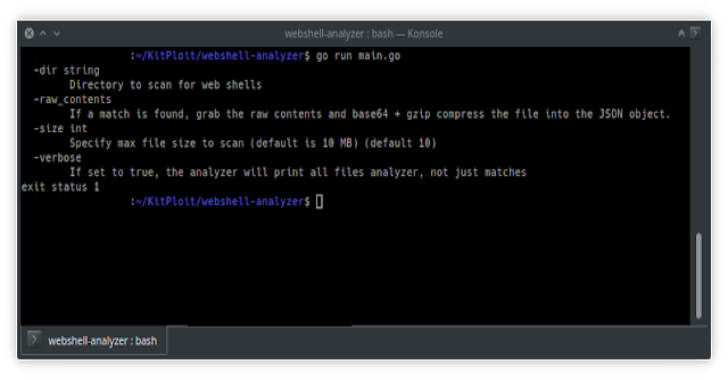
Webshell Analyzer : Web Shell Scanner & Analyzer
Webshell analyzer is a cross platform stand-alone binary built solely for the purpose of identifying, decoding, and tagging files that are suspected to be...
© kalilinuxtutorials.com 2025





.webp)
.webp)
.webp)
.webp)
.webp)

.webp)
.webp)
.webp)
.webp)