APPLICATIONS
HOT NEWS
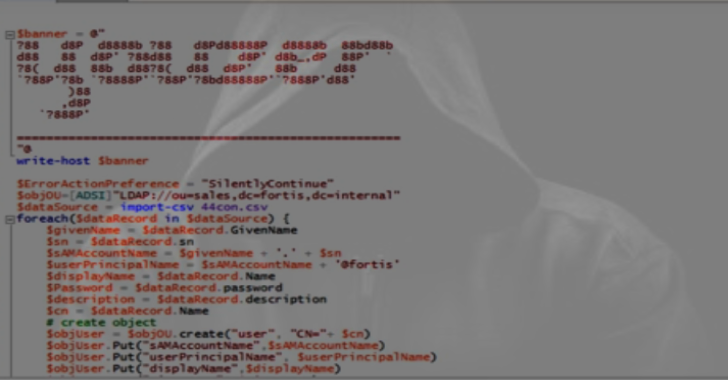
Youzer : Fake User Generator For Active Directory Environments
Fake User Generator for Active Directory Environments. The goal of Youzer is to create information rich Active Directory environments.
This uses the python3 library 'faker'...
© kalilinuxtutorials.com 2025











.webp)

.webp)
.webp)