APPLICATIONS
HOT NEWS
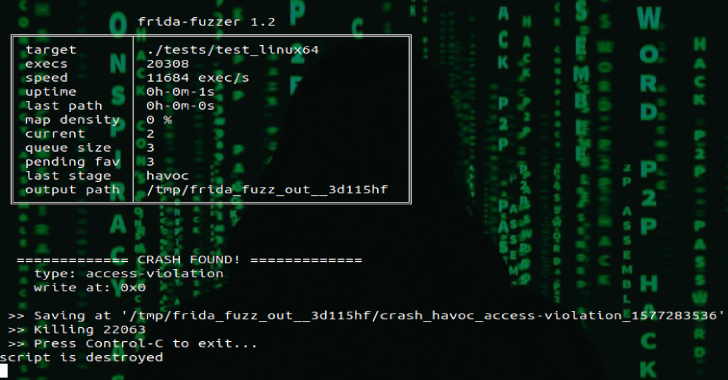
Frida-Fuzzer : Experimental Fuzzer Used For API In-Memory Fuzzing
Frida-Fuzzer is a experimental fuzzer is meant to be used for API in-memory fuzzing. The design is highly inspired and based on AFL/AFL++. ATM...
© kalilinuxtutorials.com 2025