APPLICATIONS
HOT NEWS
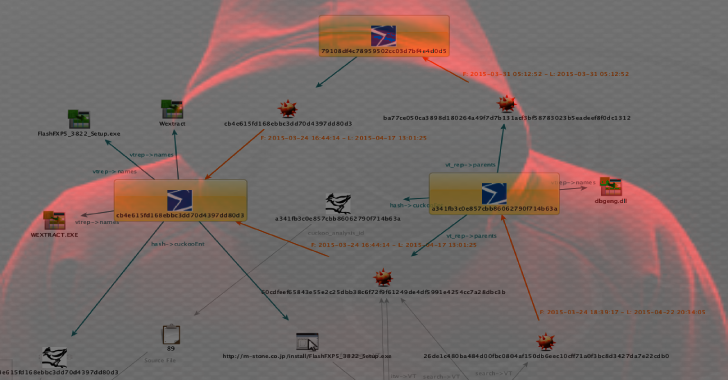
RIPVT : Virus Total API Maltego Transform Set For Canari
ripVT is a Maltego Canari transforms for Virus Total private API. Provided AS-IS, no warranties, no guarantees. No jokes in this repo. It's as...
© kalilinuxtutorials.com 2025








.webp)
.webp)




%20(1).webp)