APPLICATIONS
HOT NEWS
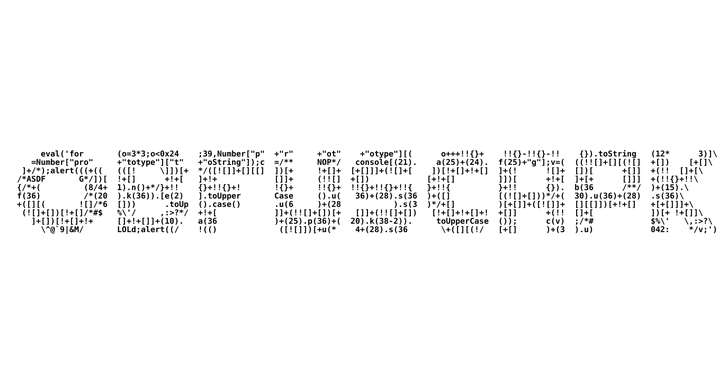
Obfuscapk : Black-Box Obfuscation Tool For Android Apps
Obfuscapk is a modular Python tool for obfuscating Android apps without needing their source code, since apktool is used to decompile the original apk file and...
© kalilinuxtutorials.com 2025





.webp)
.webp)
.webp)
.webp)
.webp)
.webp)

.webp)

.webp)