APPLICATIONS
HOT NEWS
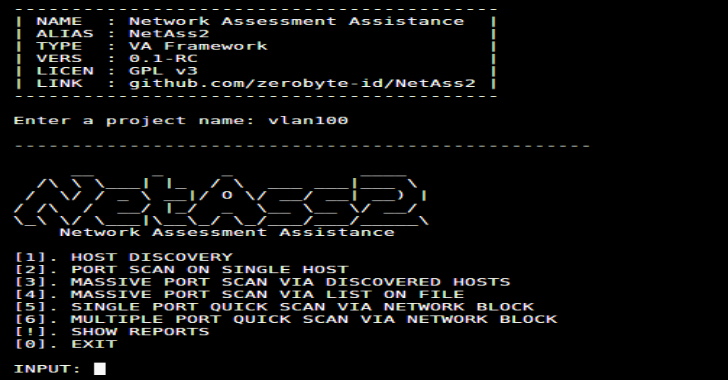
NetAss2 : Network Assessment Assistance Framework (PenTest Toolkit)
NetAss2 is a easier network scanning with NetAss2 (Network Assessment Assistance Framework). Make it easy for Pentester to do penetration testing on network.
Dependencies
nmap (tool)zmap...
© kalilinuxtutorials.com 2025